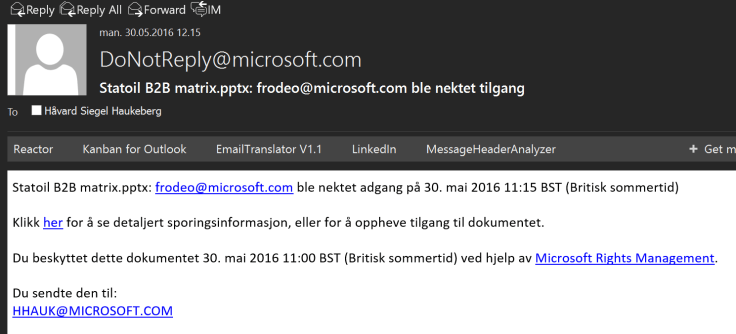
What will the user see if he puts a Azure RMS protected file on SharePoint online?
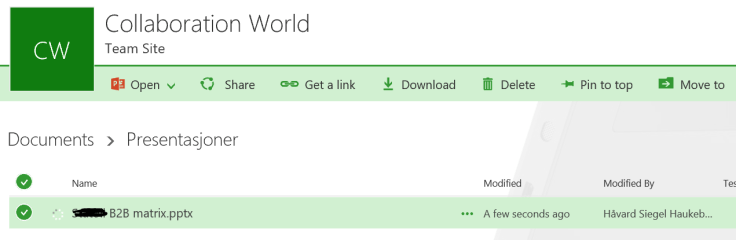
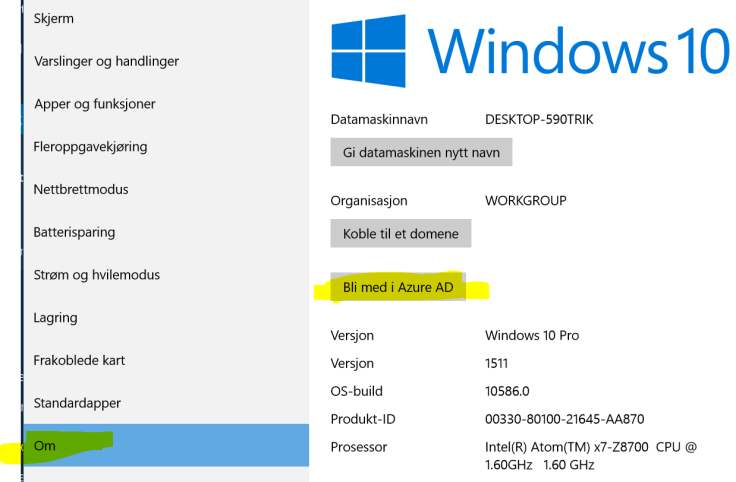
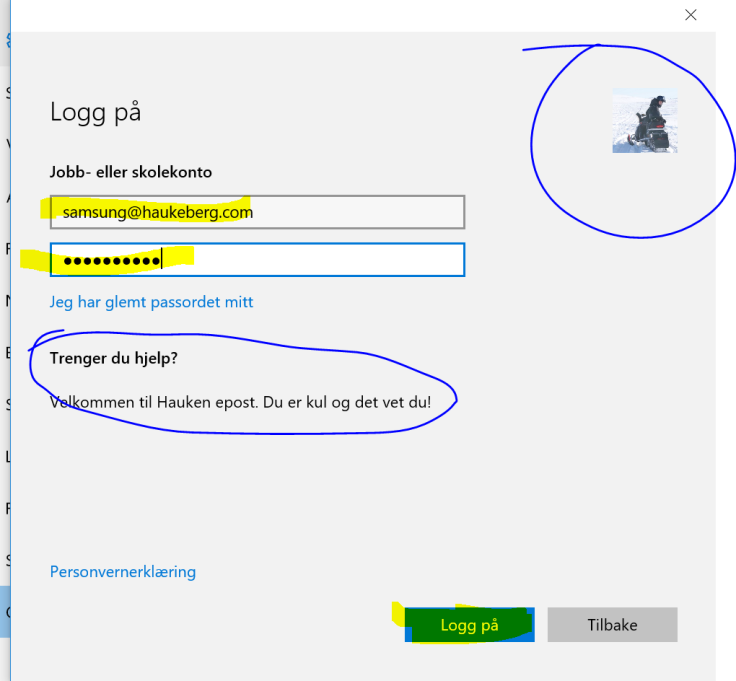
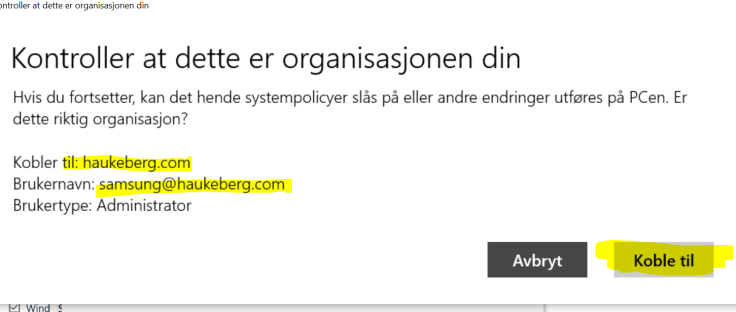
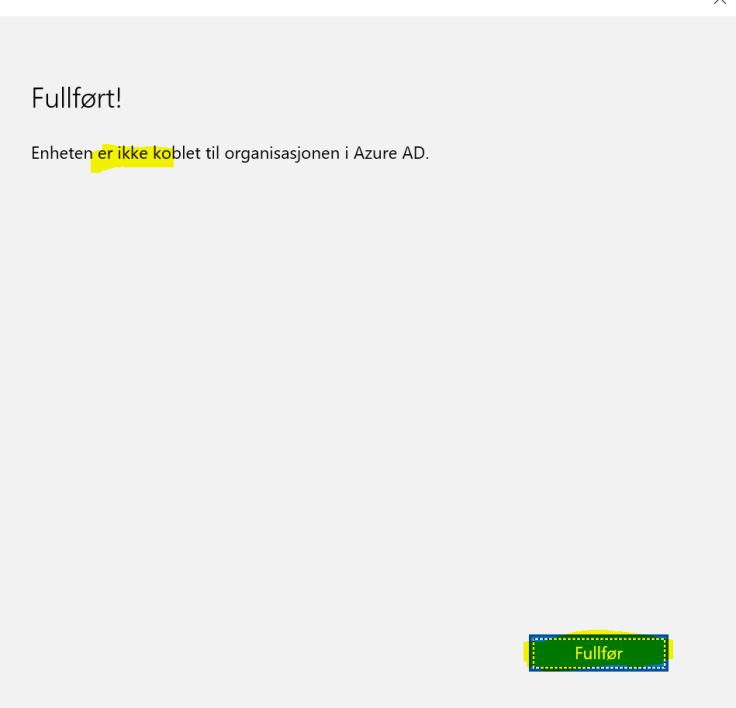
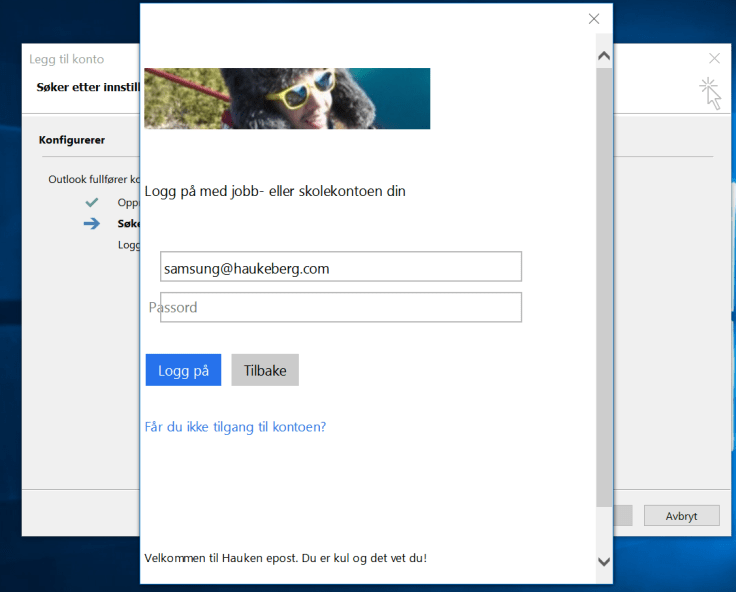
Setup:
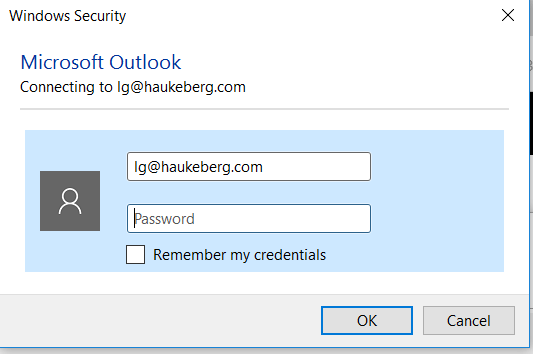
- Azure RMS account and document owner: hsh@haukeberg.com
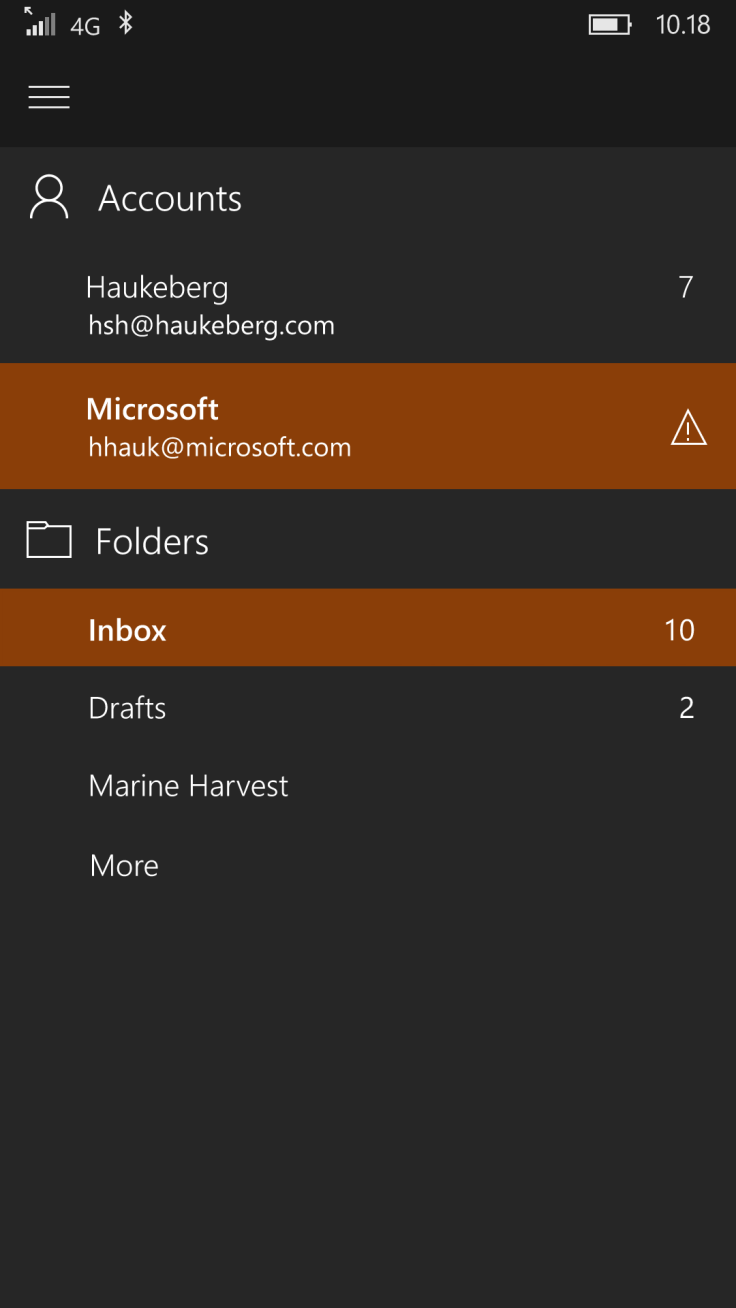
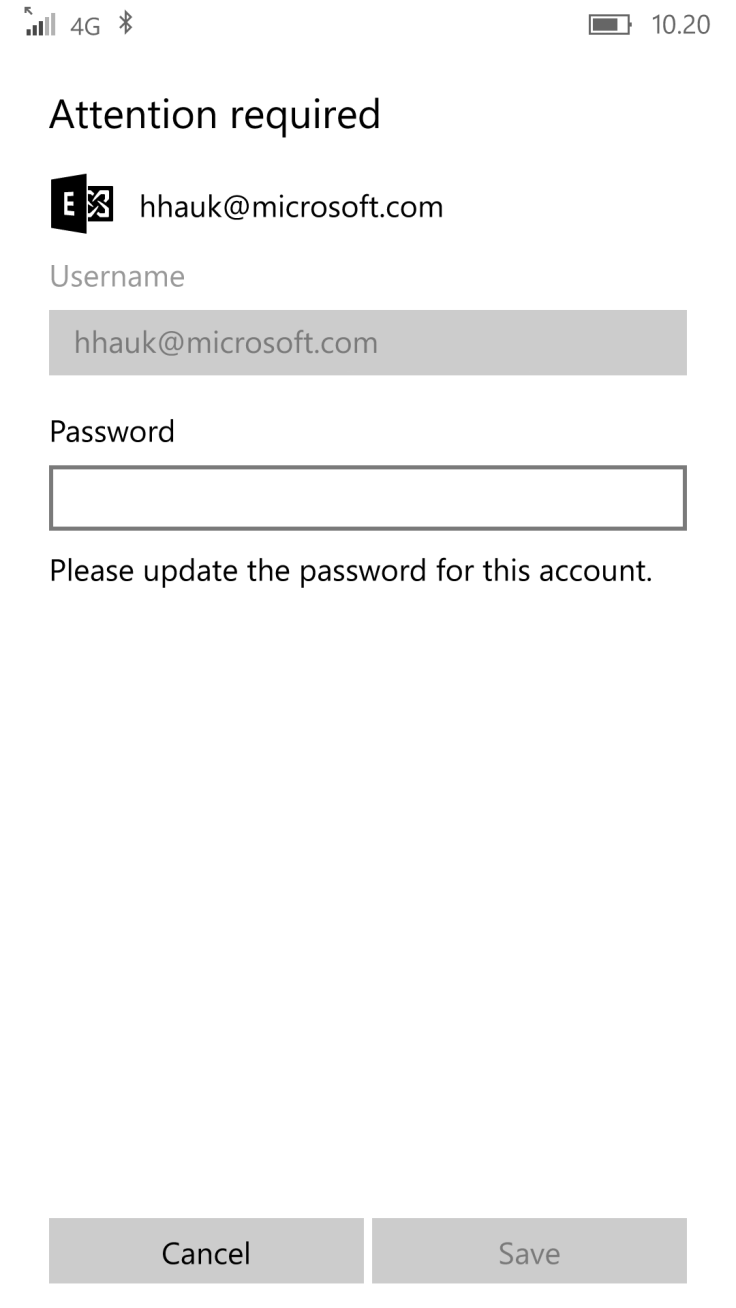
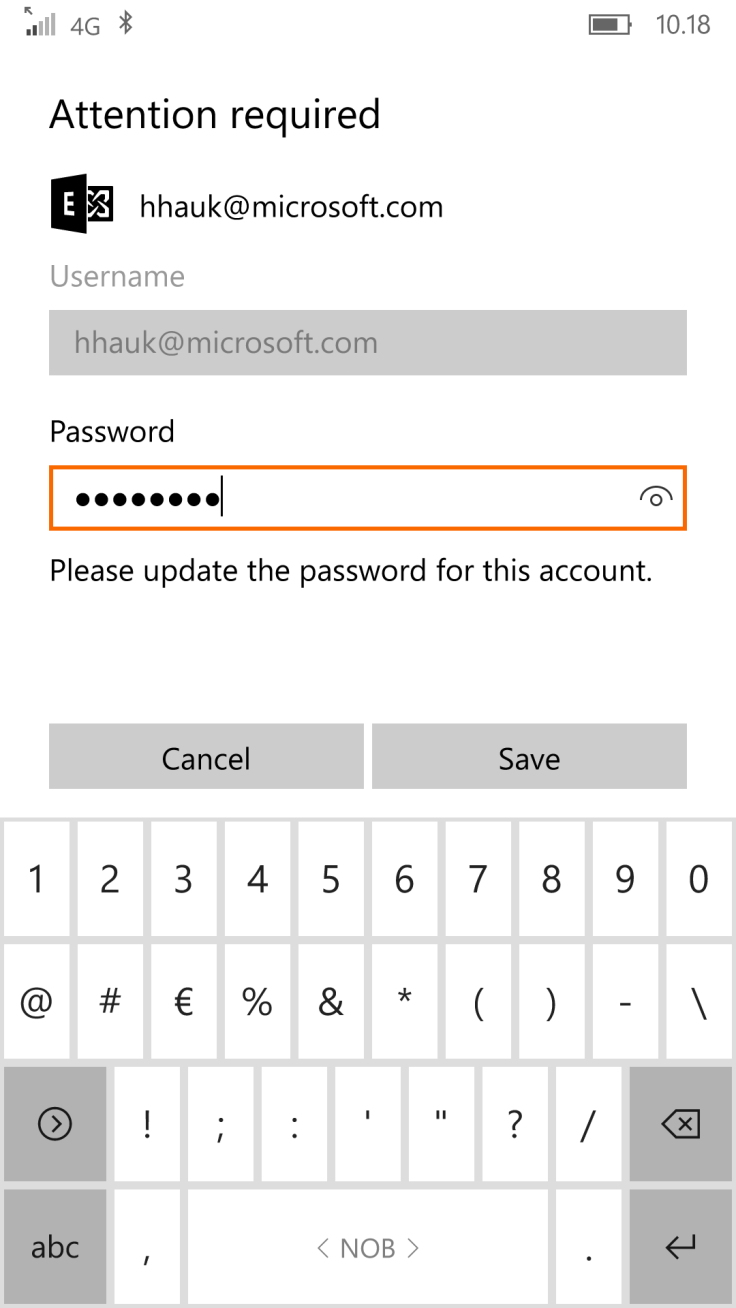
- SharePoint Online accont: hhauk@microsoft.com
- Document shared with hhauk@microsoft.com read only
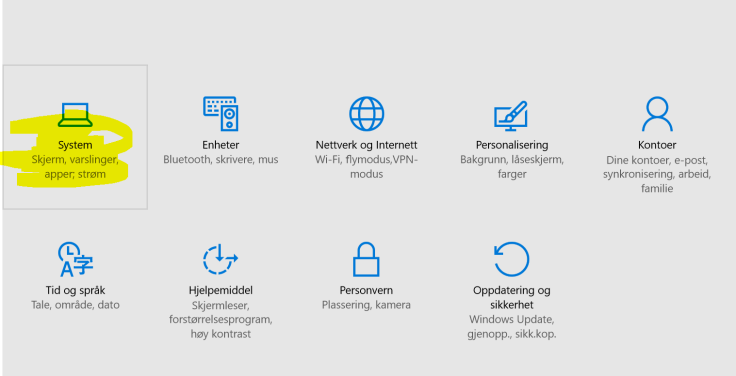
- Do not worry about language (you can get this software in your language)
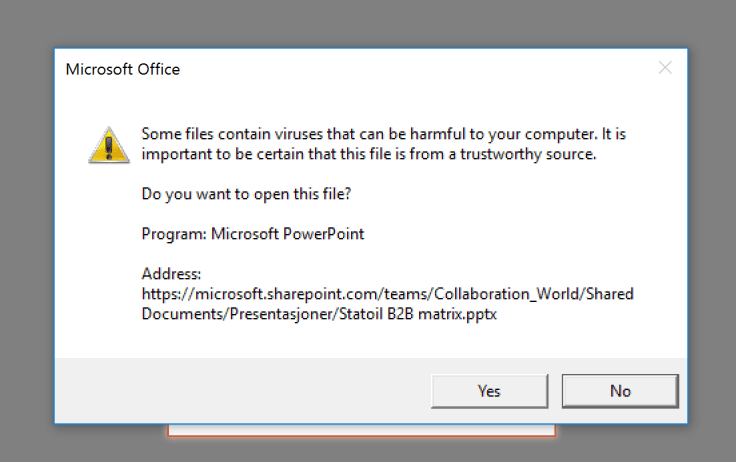
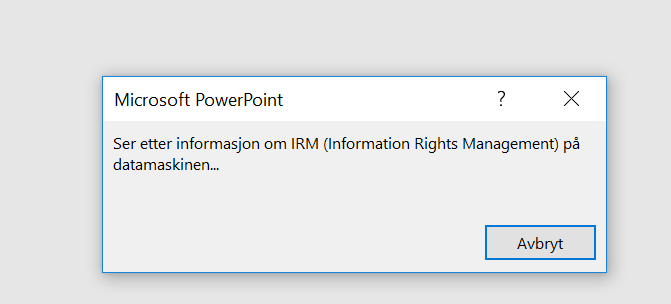
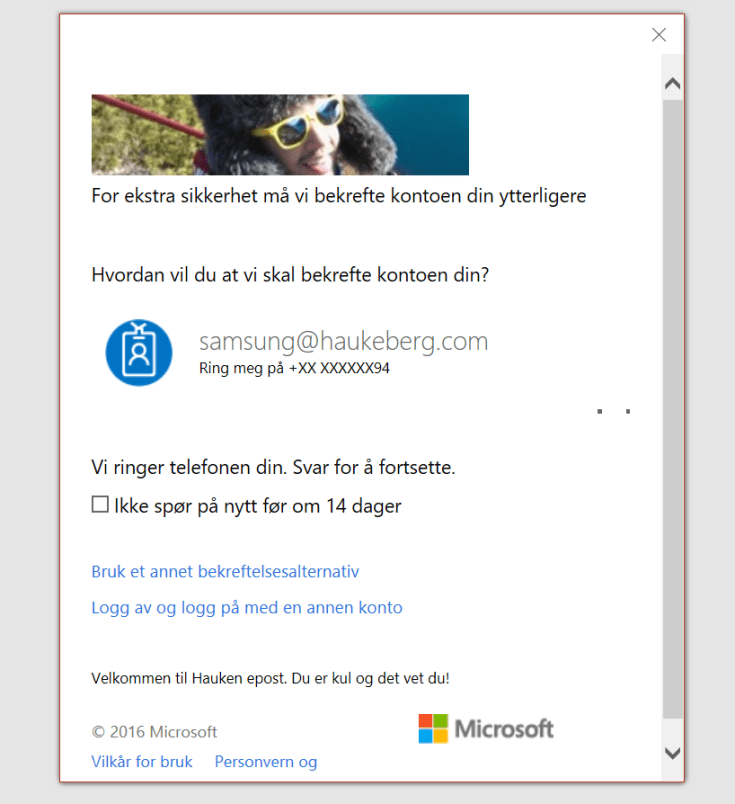
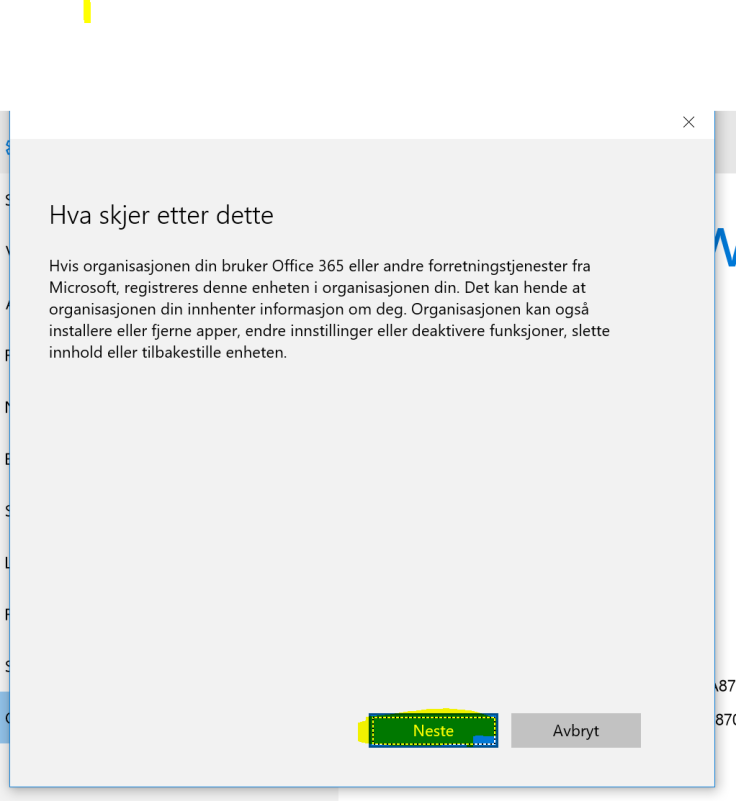
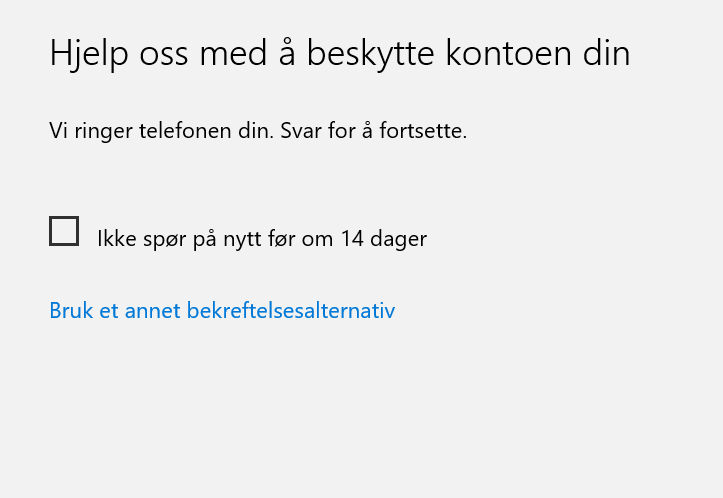
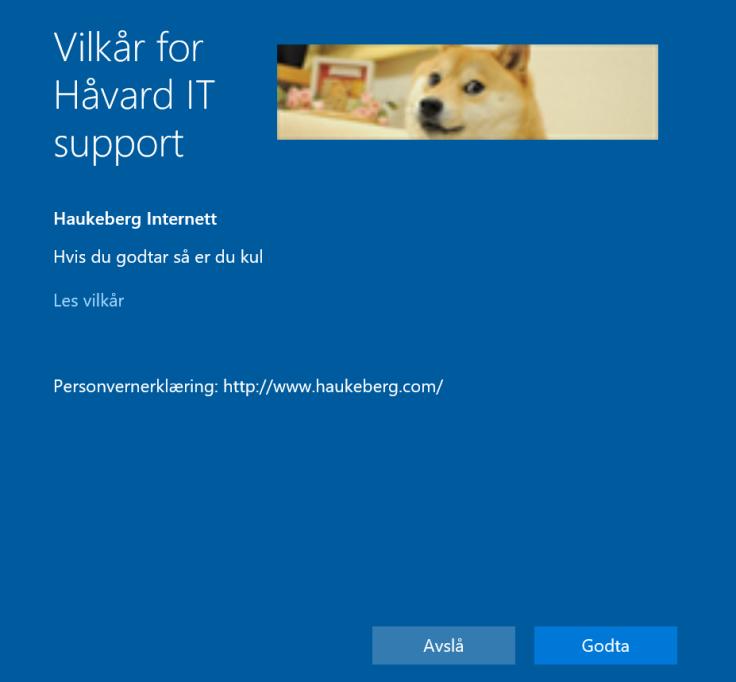
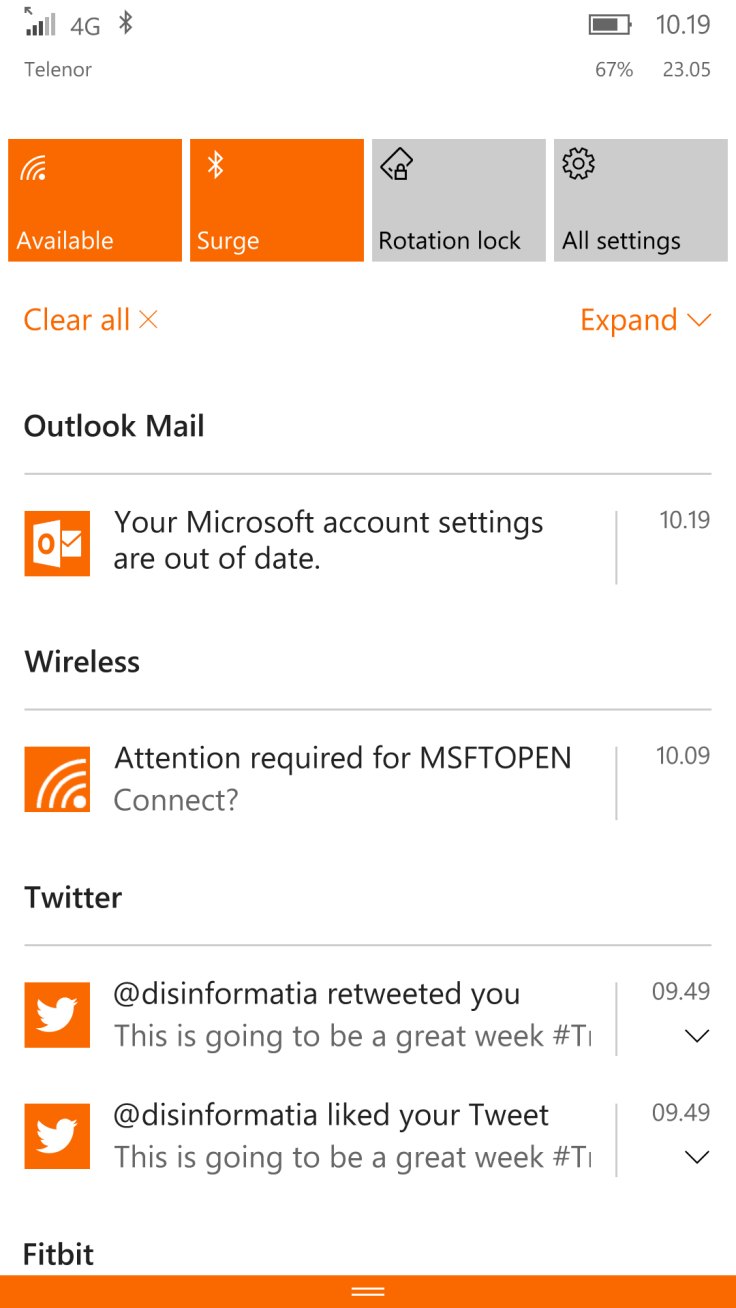
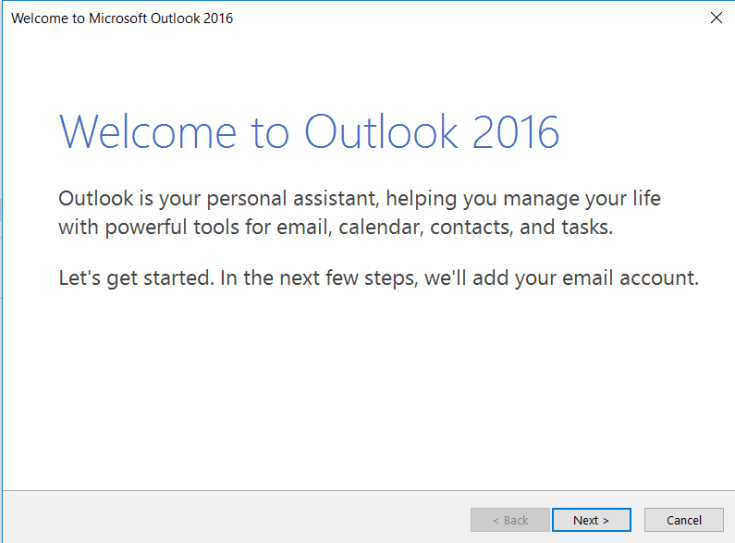
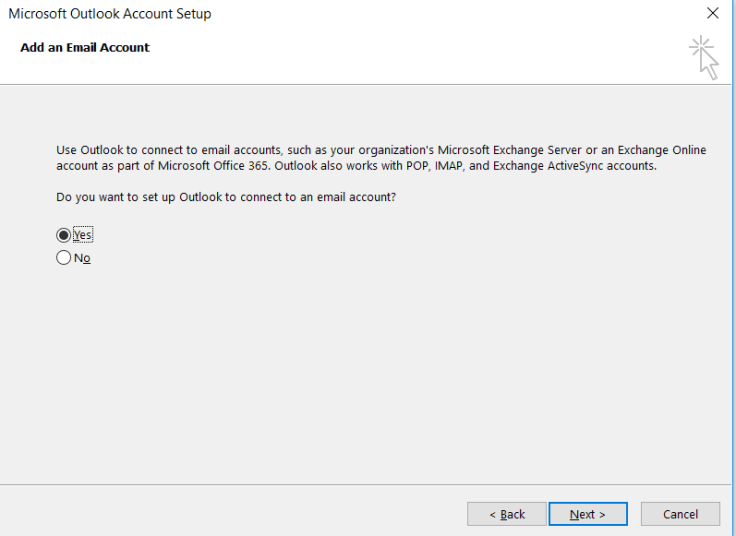
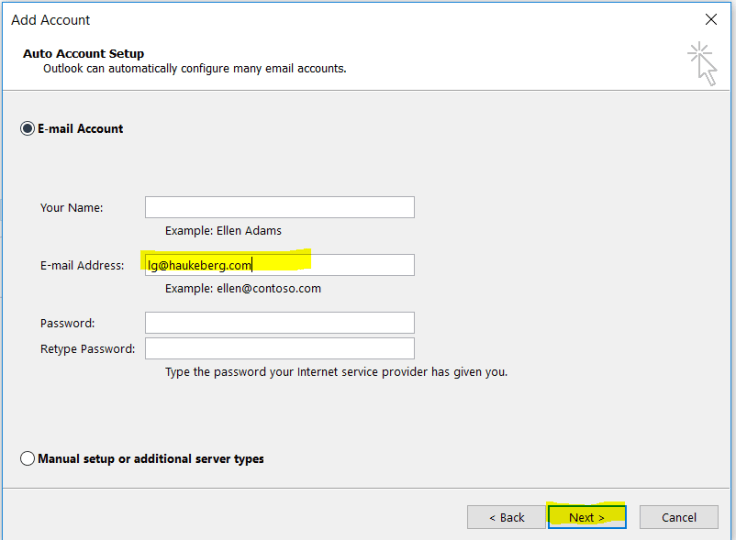
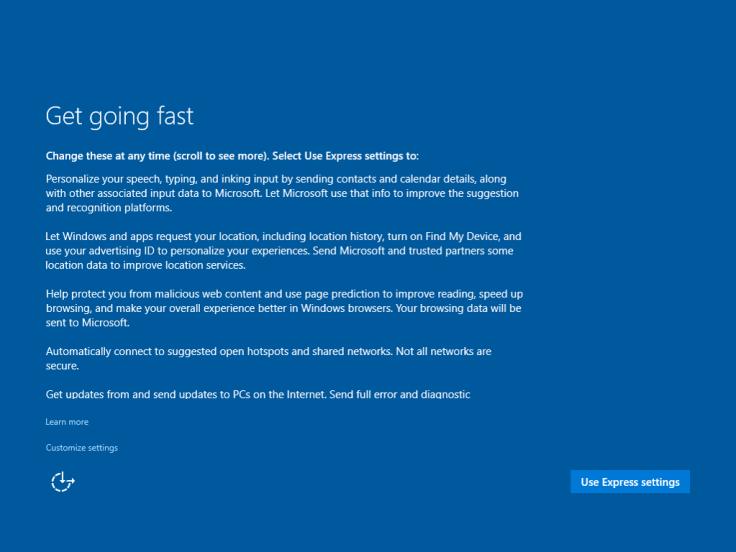
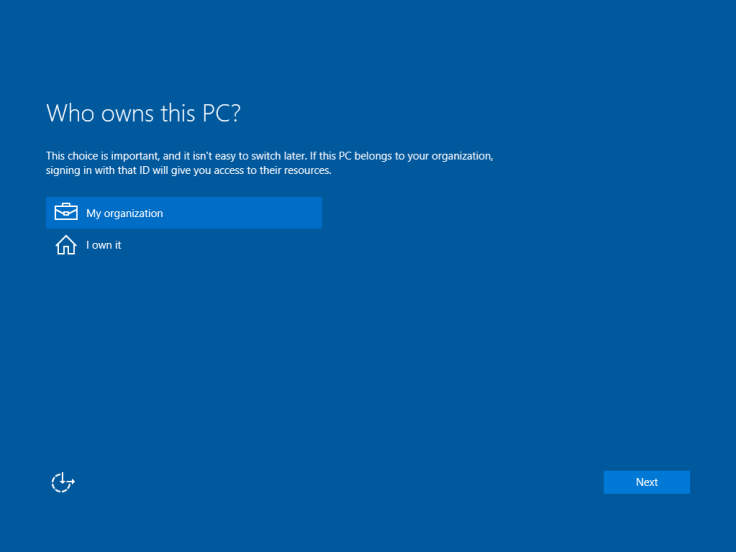
Here is what happens:
















You must be logged in to post a comment.