This post will now be a list of Sway’s for enrollment into Azure AD and Intune.
- Windows 10 Pro Azure AD join
- Windows 10 enterprise Education Azure AD Join
- Azure MFA enrollment
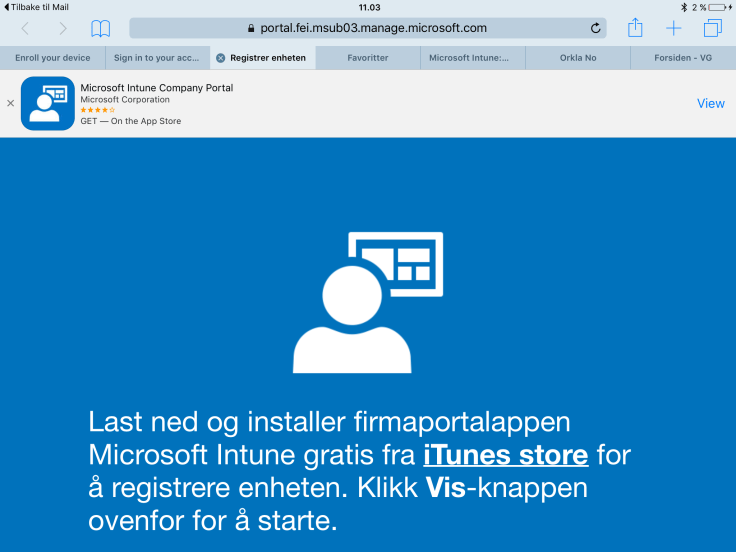
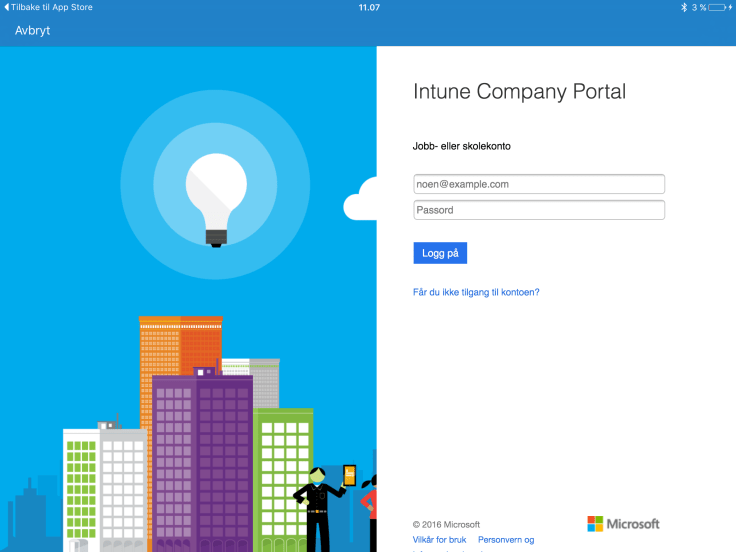
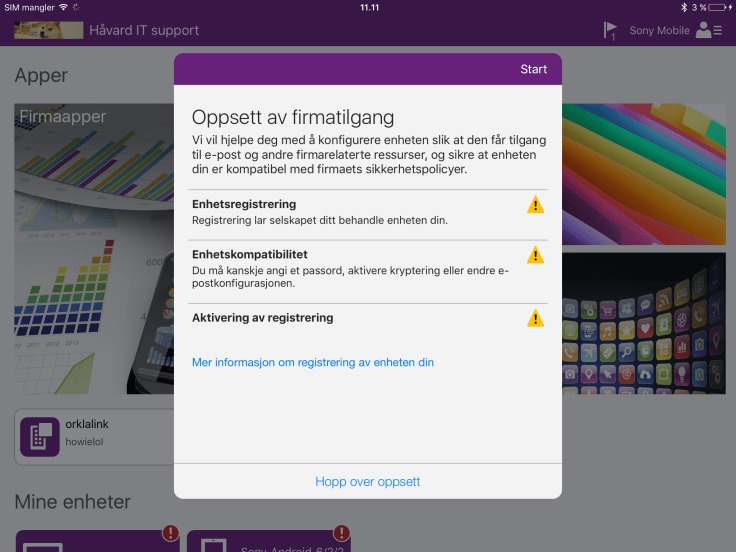
- Ipad into intune
Once a end user has enrolled a Android device it will shortly show up in the Intune portal.
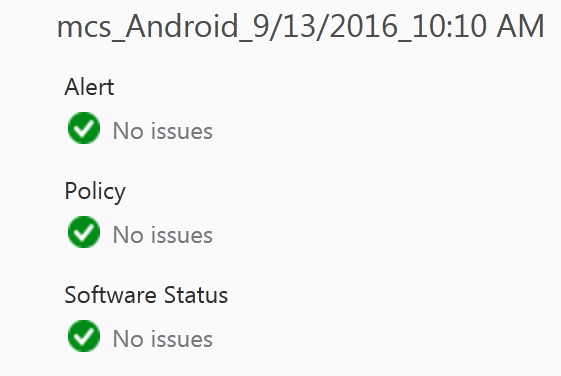
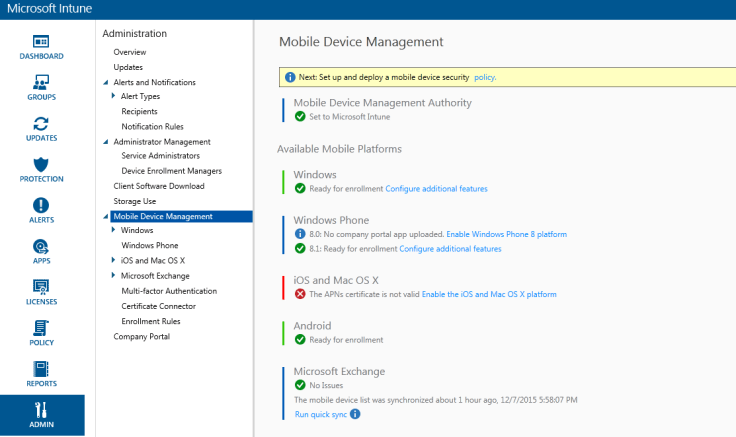
This is what a healthy Device should look like in the Intune Portal http://manage.microsoft.com :
If you need device info, the Intune MDM agent will pull information from the device and display some of it here in the general info tab just right to the health status
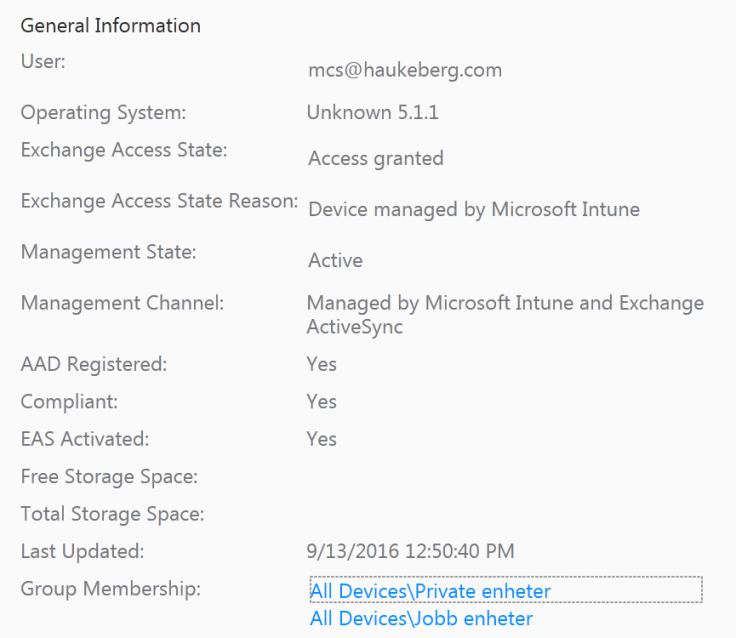
There are many different Android phones out there. They all provide info to Intune MDM differently. Here Sony is not able to convey the OS name correctly to Intune.

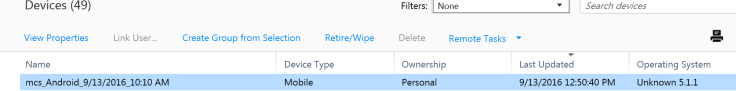
In the device list you can see and sort the list of devices on most of the general information.
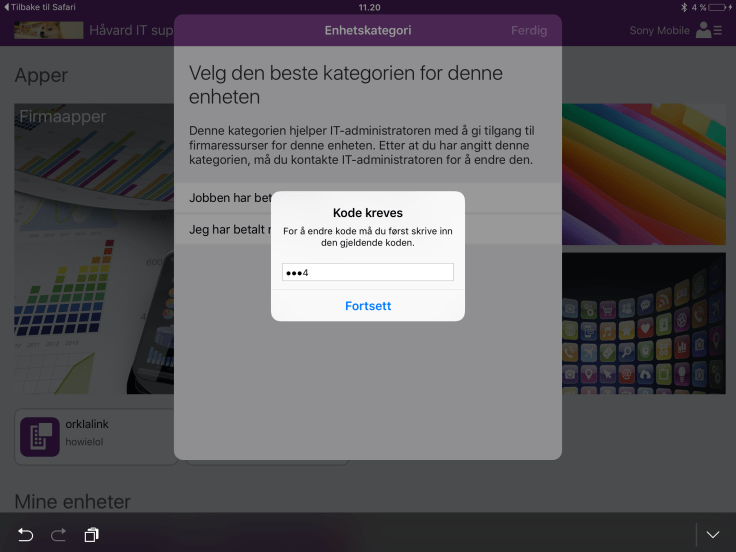
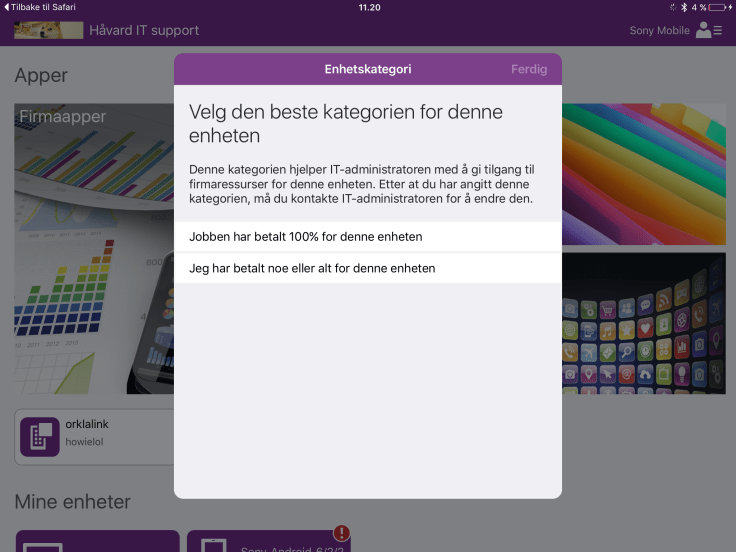
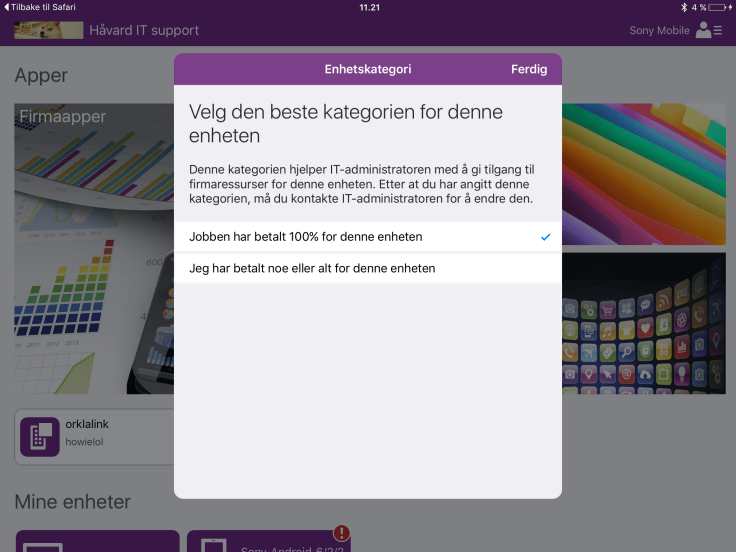
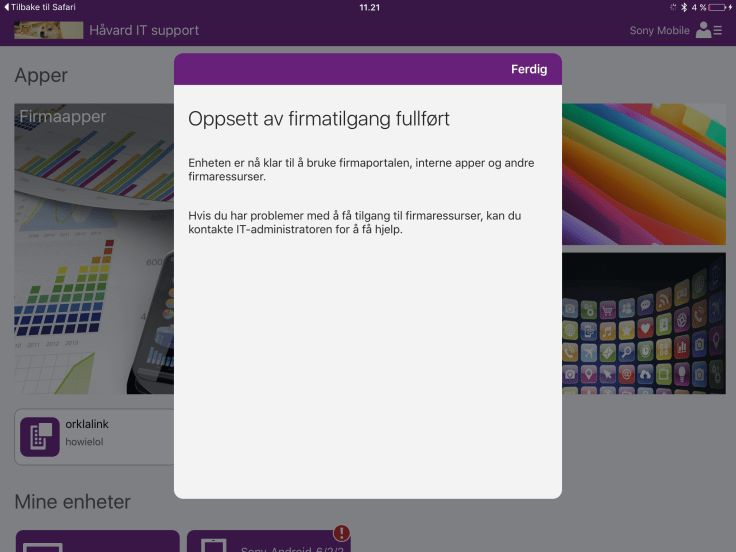
When the end user enrolled this Sony Android Device he was prompted to group his device himself into a group. This group is displayed here. I have named this group myeself in the Intune portal. You could name it anything other than personal if you want to.

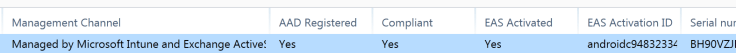
Management channel should be set to intune or intune and EAS when your device is enrolled. We should also se the Compliant status. If it is not compliant, check your compliance policies in intune policy tab or make sure that you have made the device compliant e.g. enabled PIN or encryption/screen lock +++
If your device is not compliant it will be blocked from exchange when you run Conditional Access.
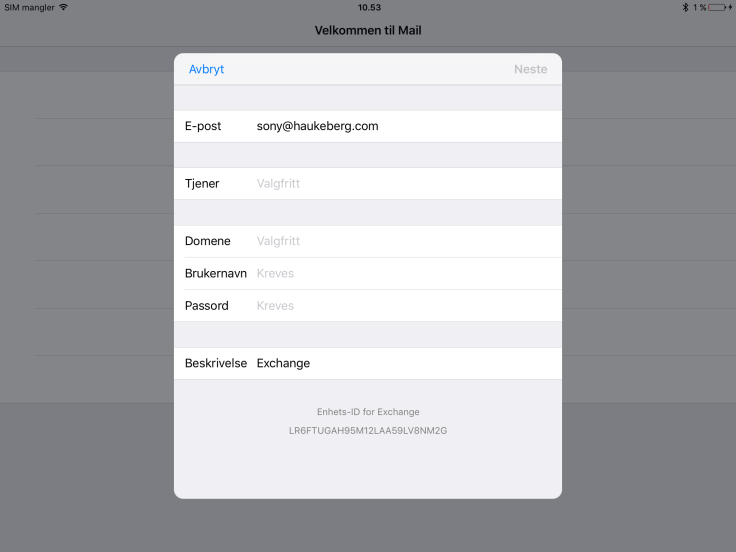
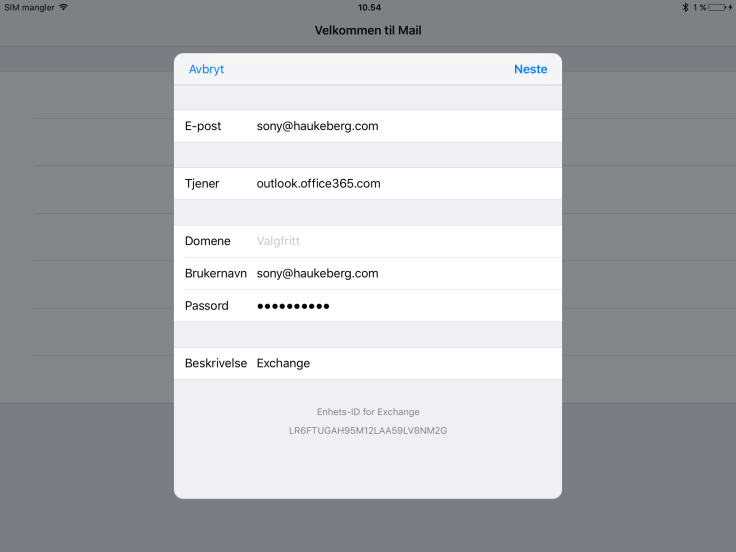
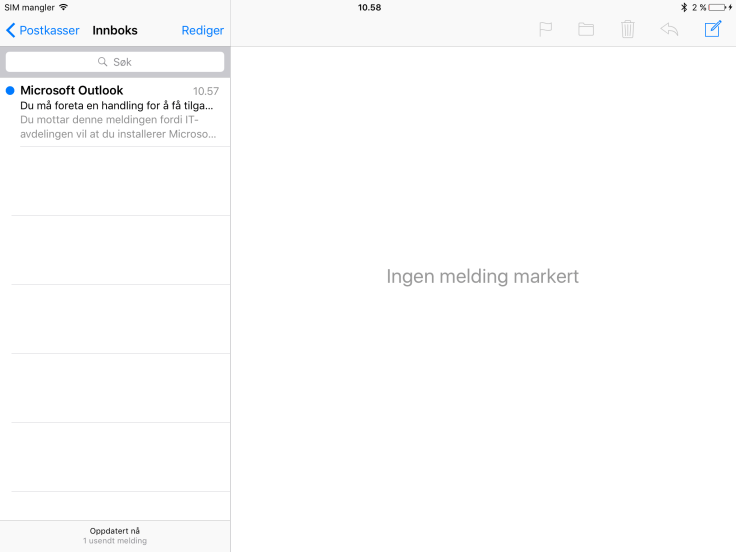
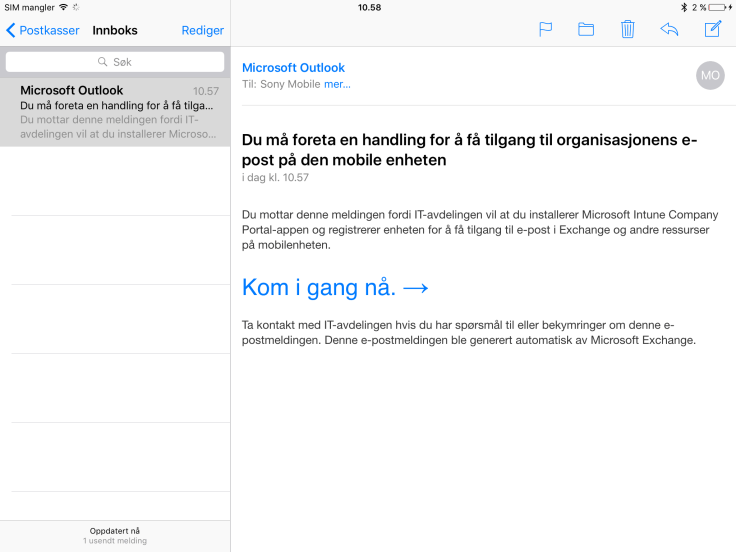
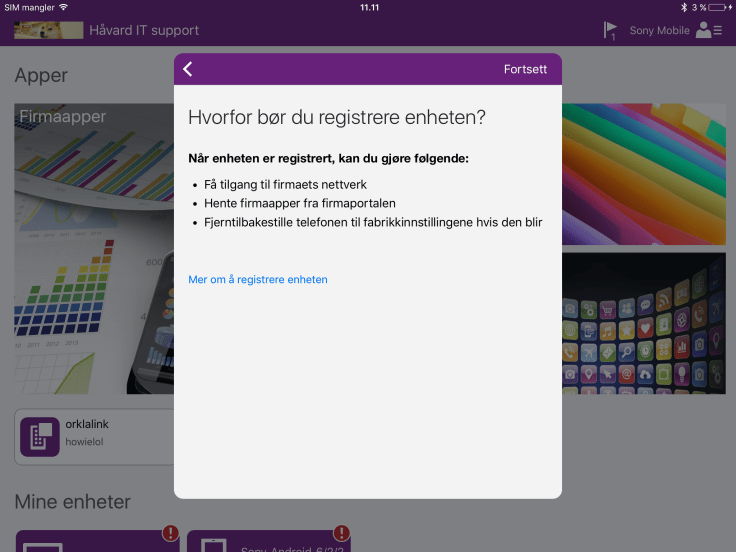
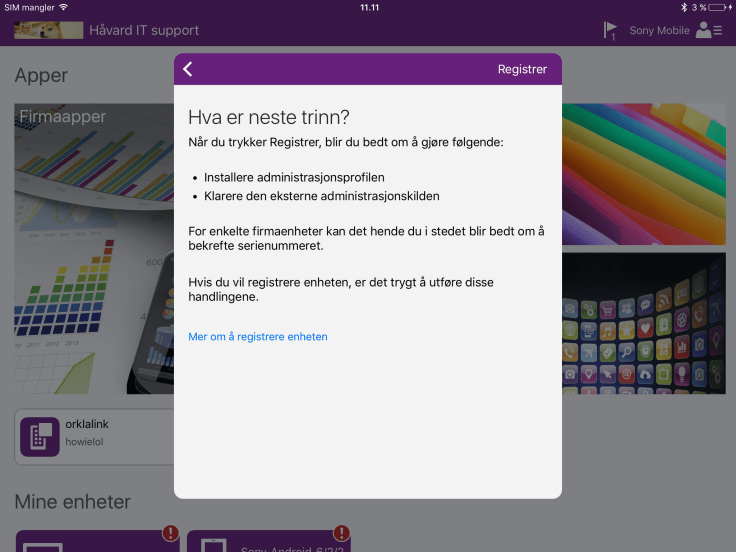
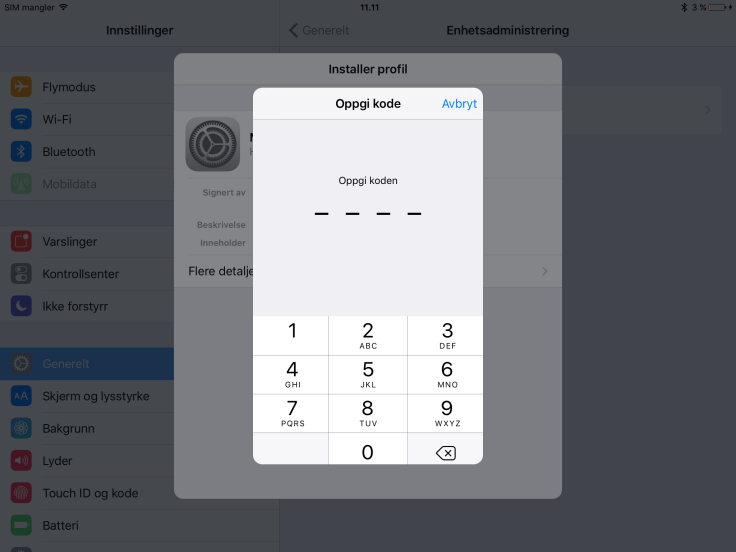
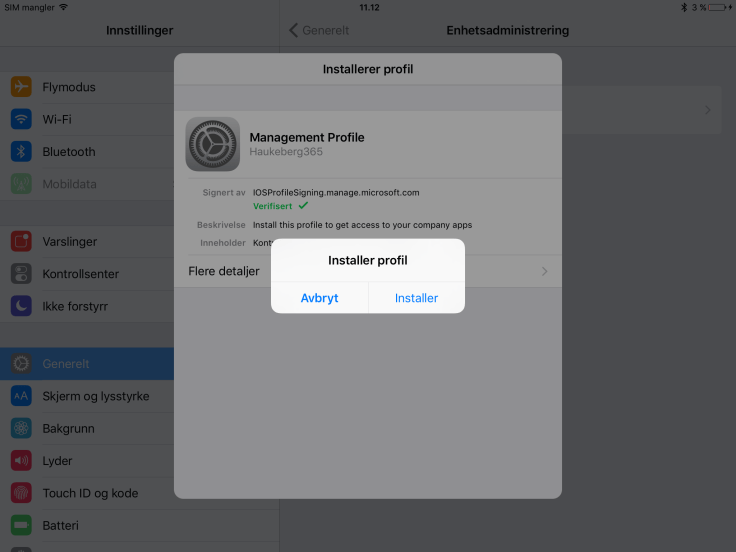
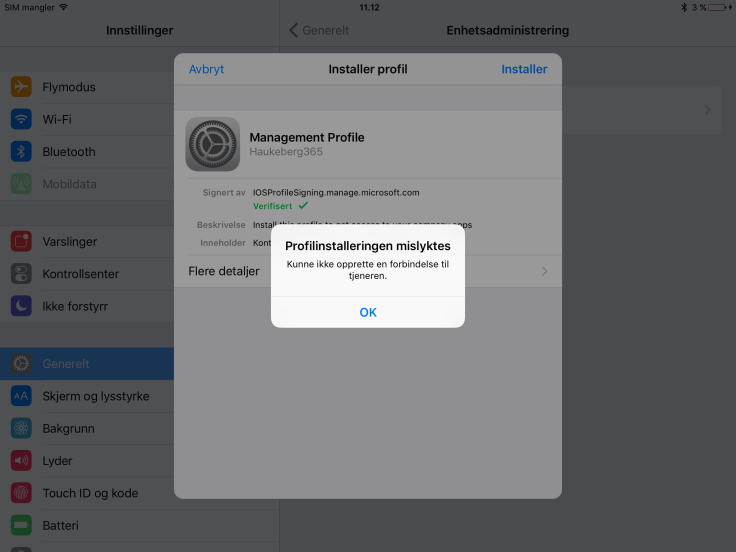
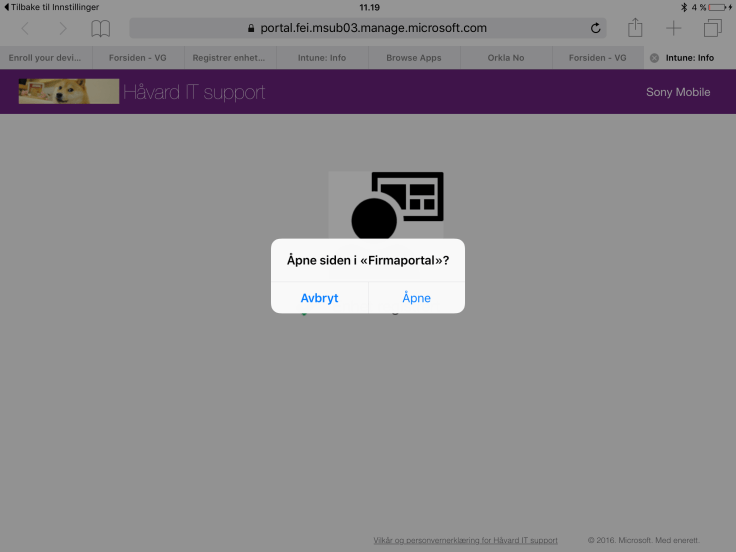
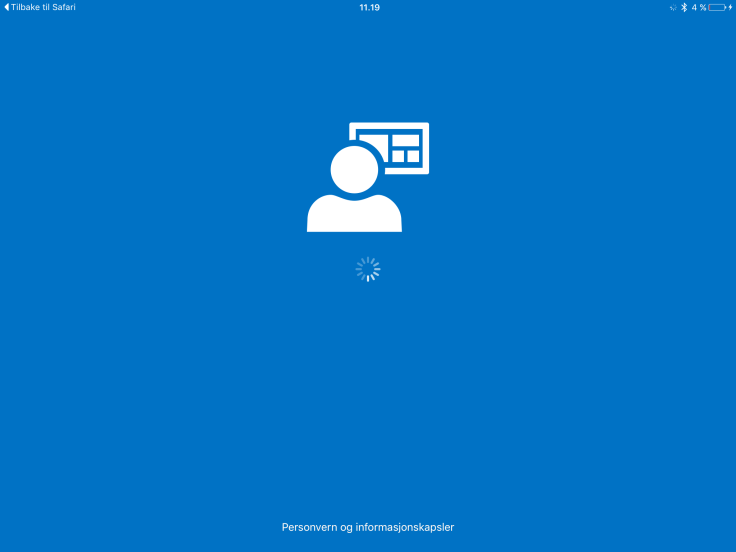
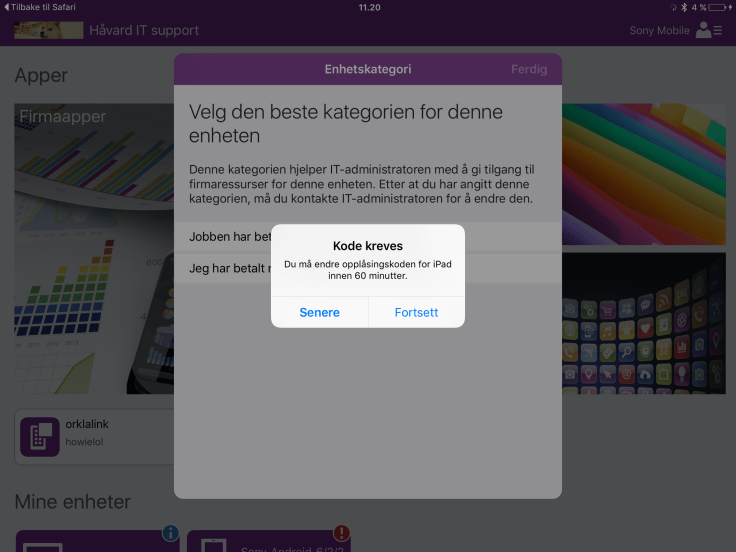
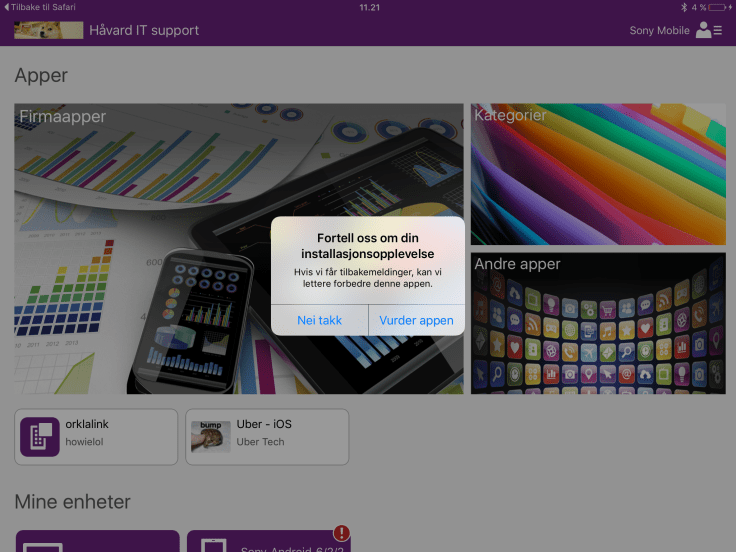
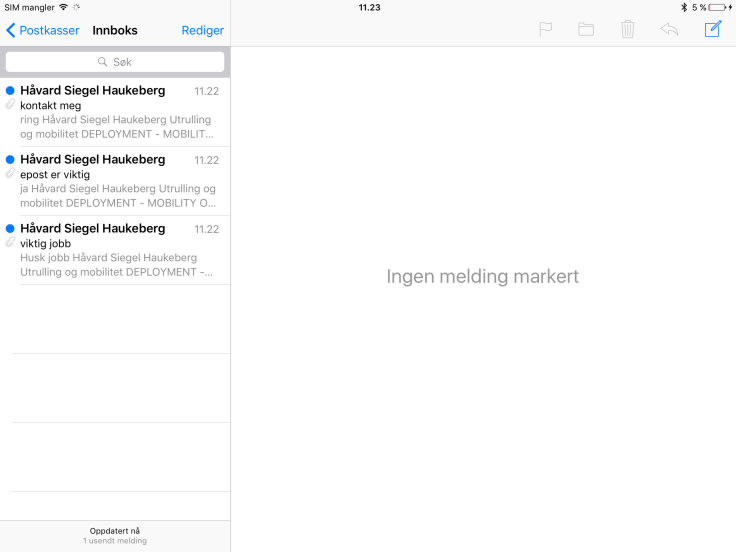
Here is a complete set of screen dumps which the end user will have to see/do in order to enroll a iOS device into Intune.










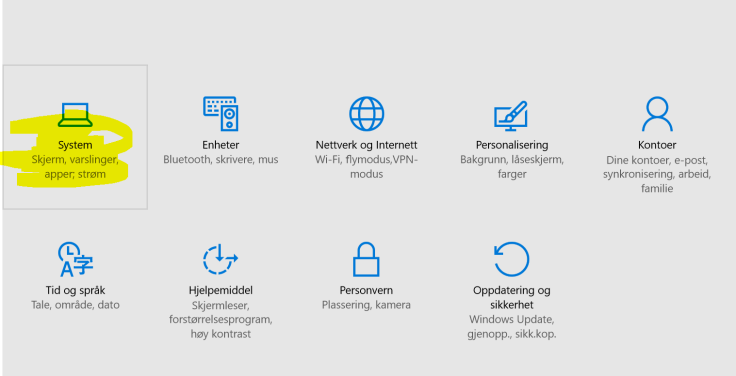
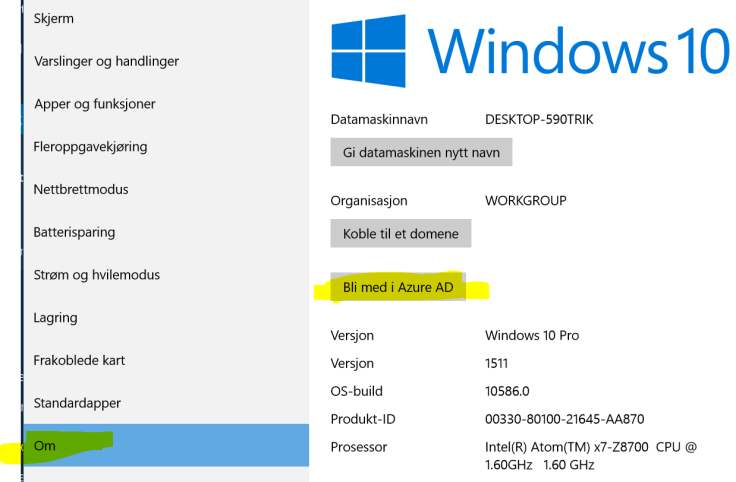
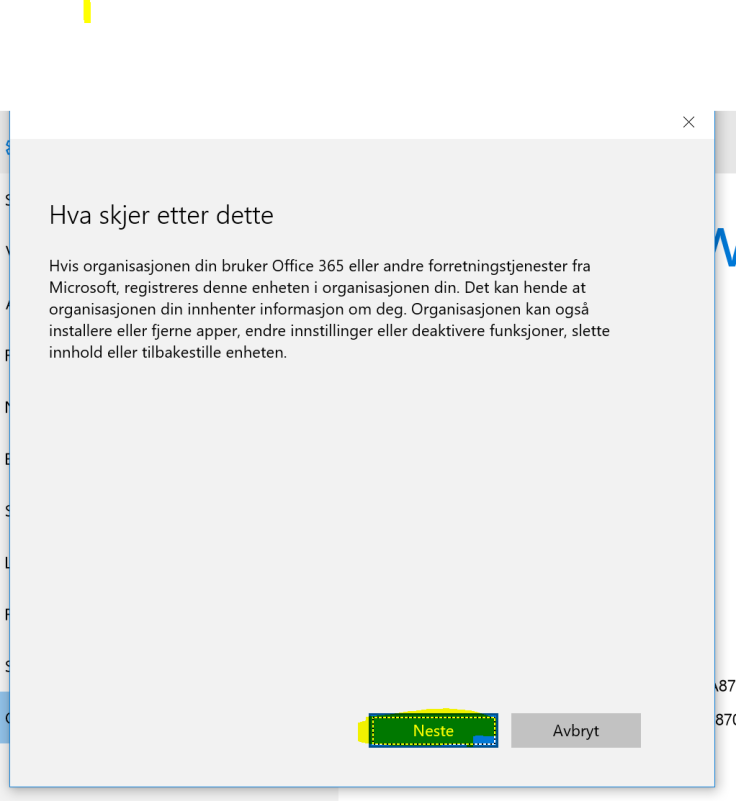
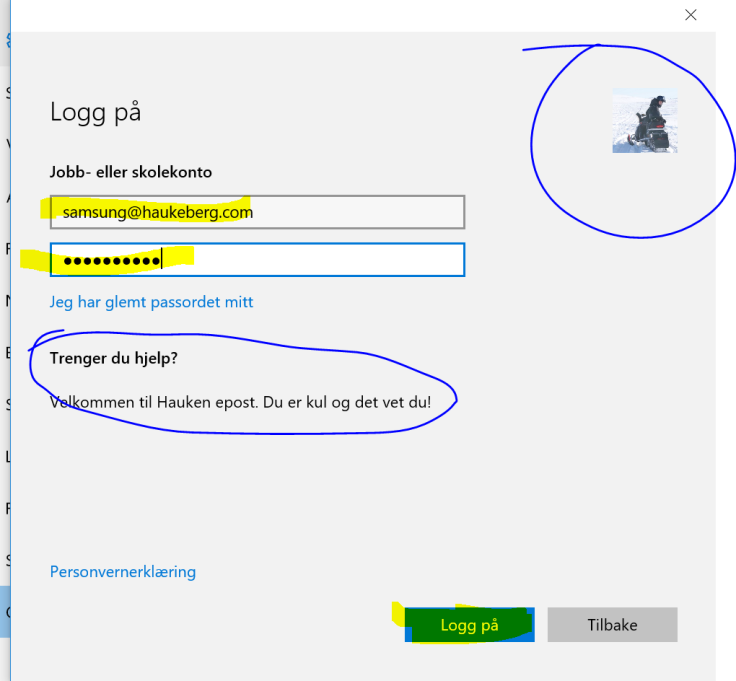
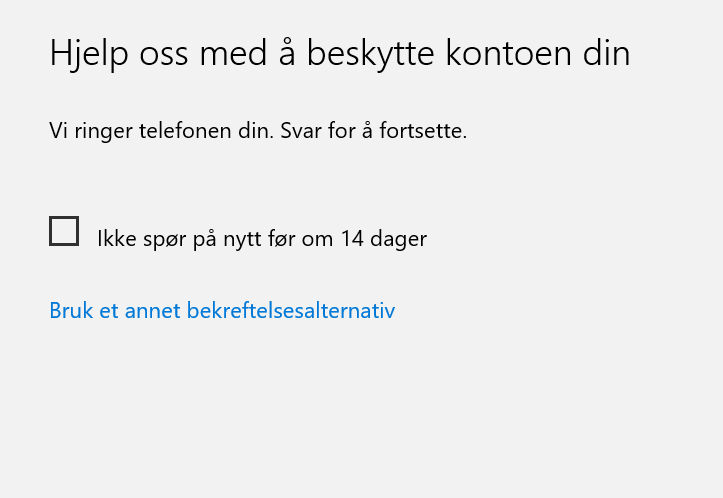
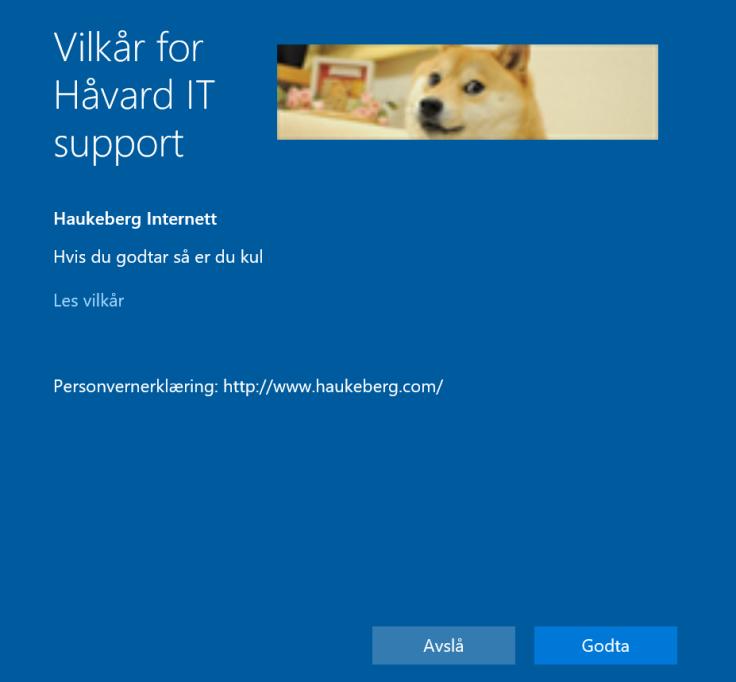
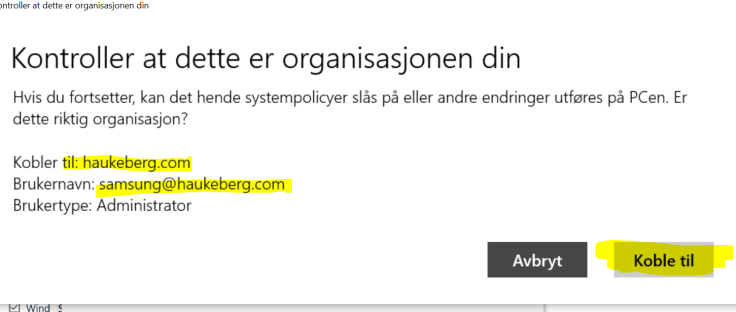
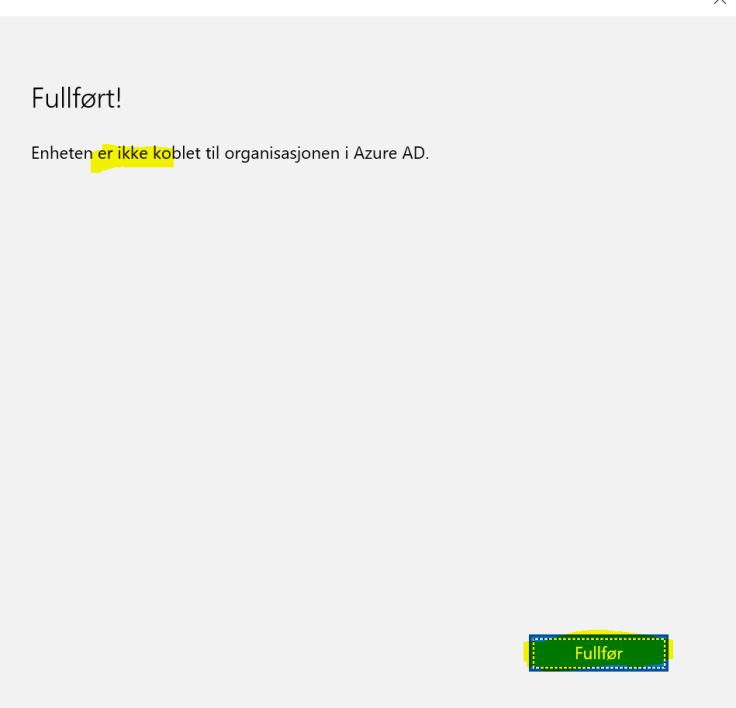
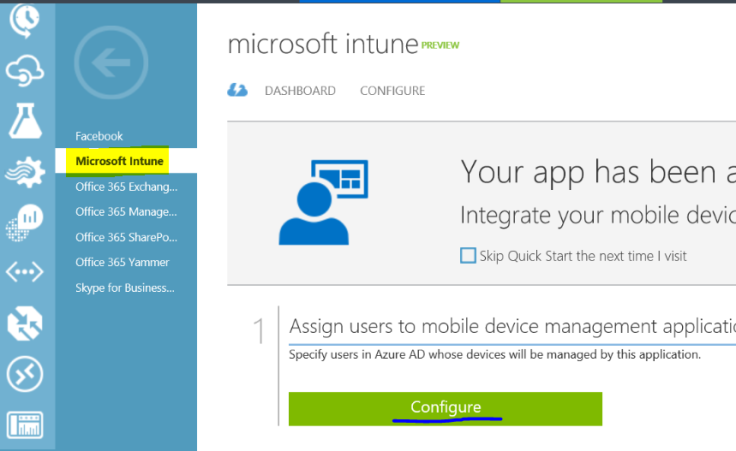
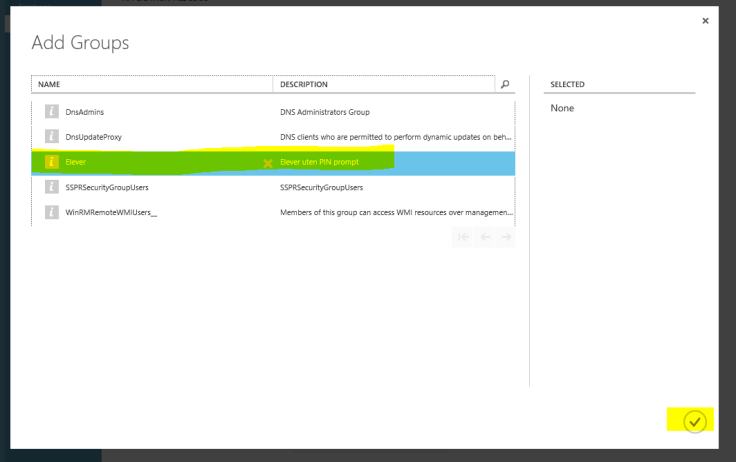
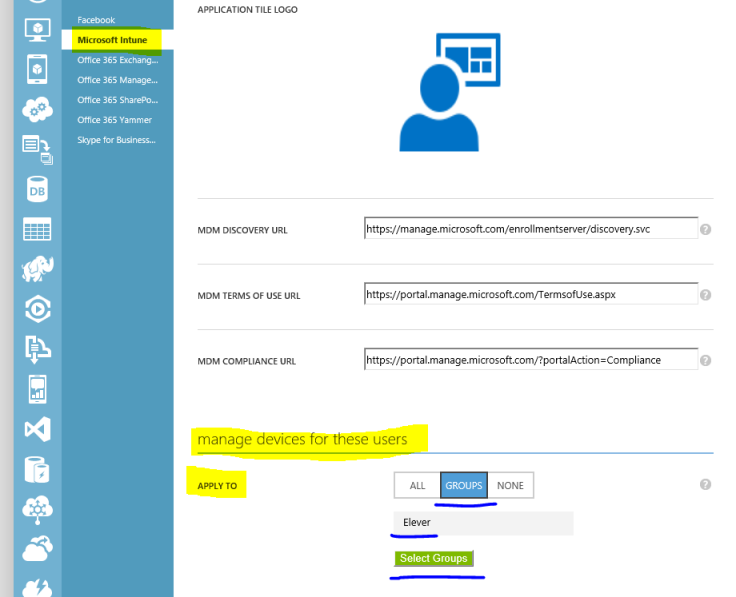
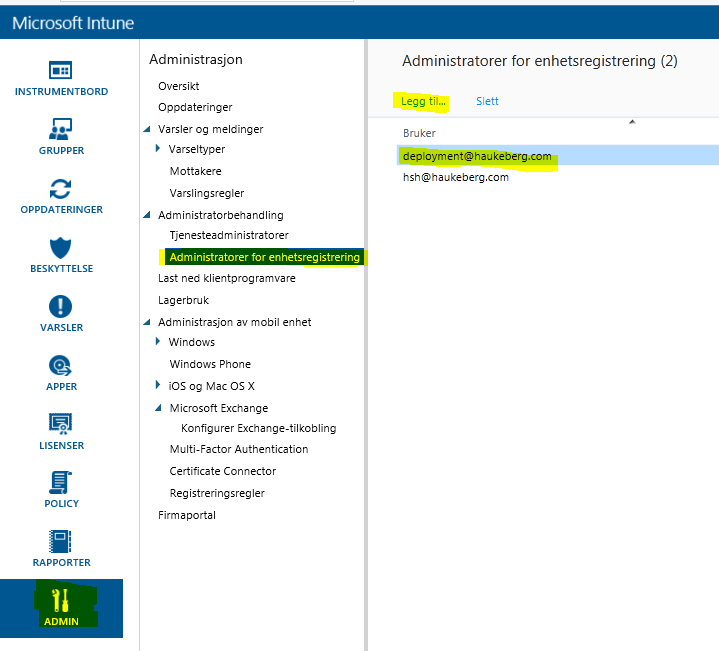
This is how you both join Azure AD and enroll for MDM. Your admin need to have configured Automatic MDM enrollment into intune over at http://manage.windowsazure.com for this to work.
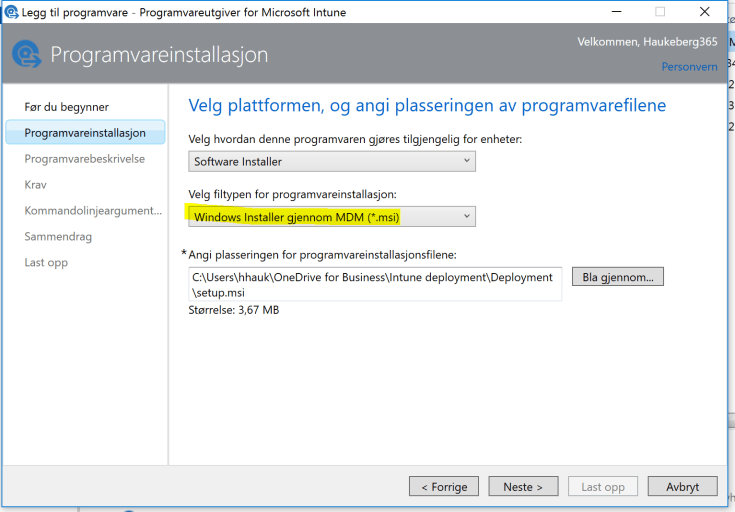
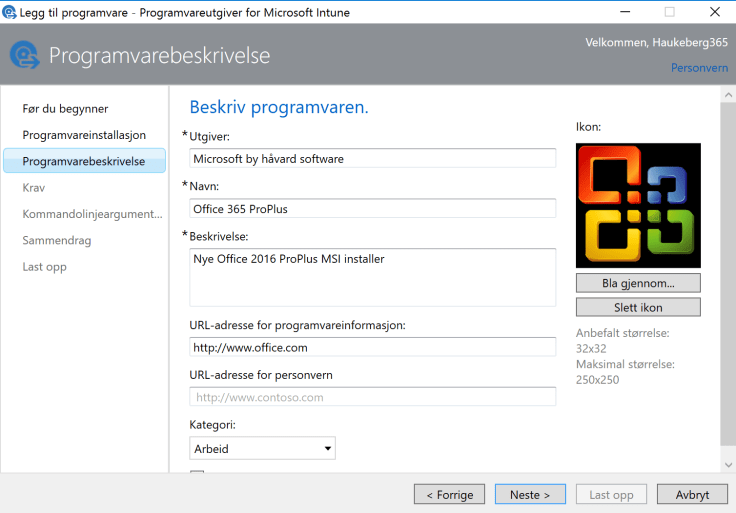
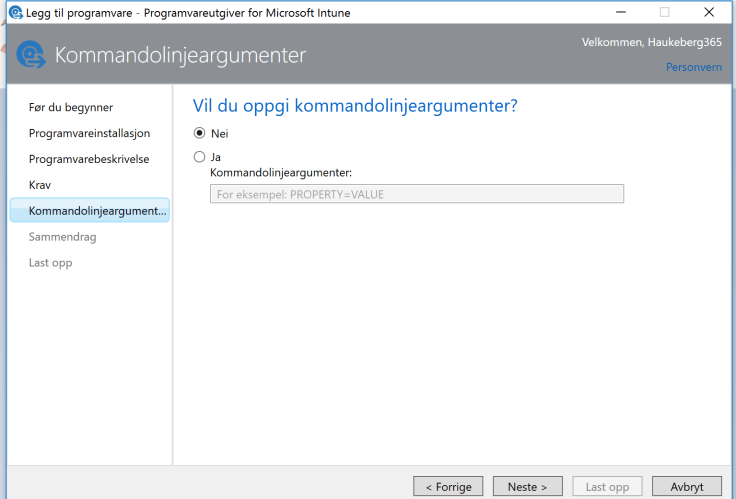
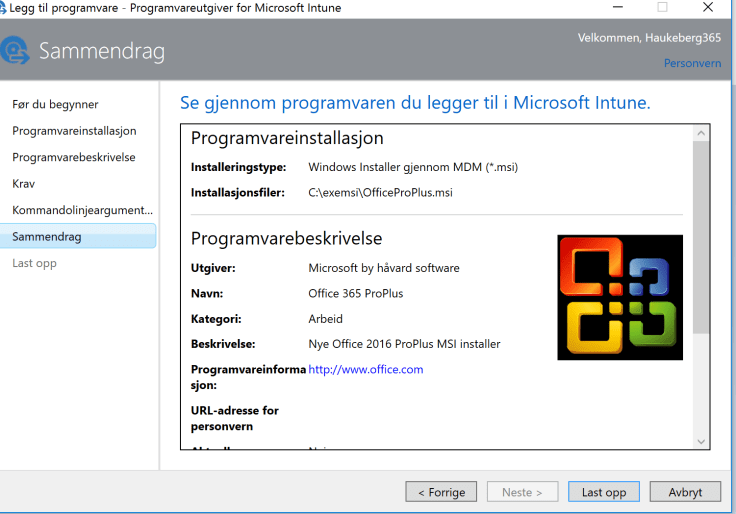
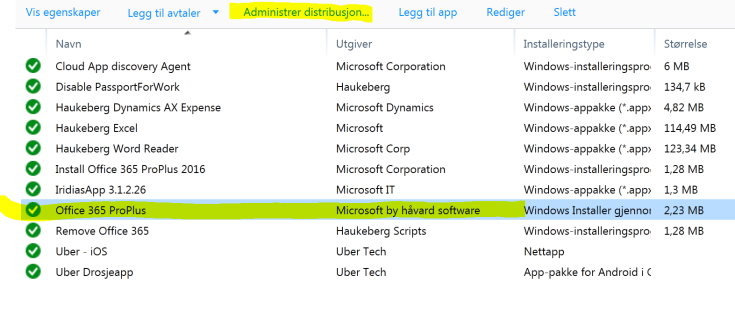
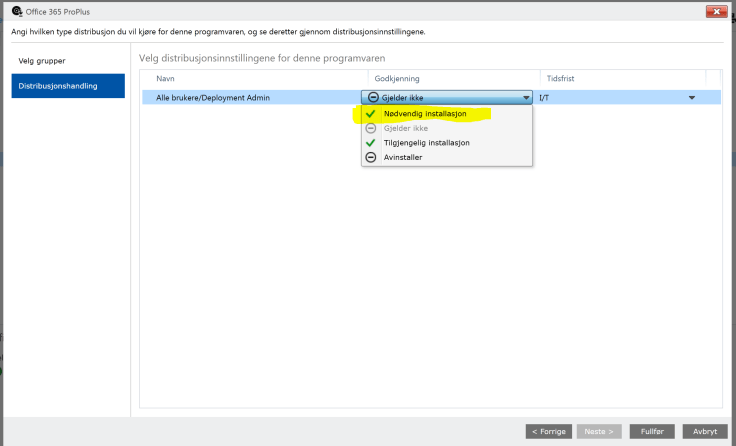
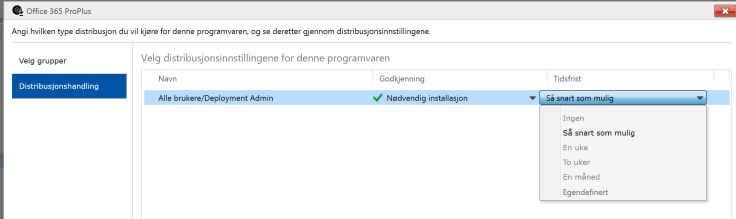
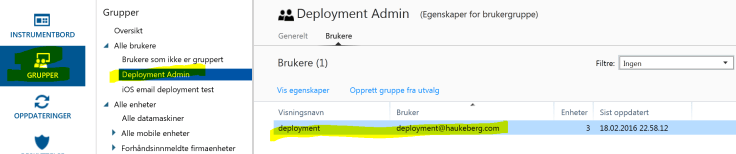
I have wrapped a EXE file (OfficeProPlus click 2 run) in a MSI wrapper. I have used a Certificate and signed the MSI and now I am going to use Microsoft Intune to push out the installation on PC’s.
Go to manage.microsoft.com and click Apps->Select Apps->Click Add an App
Launch the software wizard and log on.


You can join Azure AD and use the Intune device agent for MDM and not the MDM channel when you enroll. It is a bit tricky and require manual touch on the device.
The best experience is to include the Intune agent in the Windows Image. If can not do this then here is how:
In Azure AD:
In Intune:
On the Device:
Dersom du har koblet Intune til Office 365 så må du bruke Intune til å styre dine MDM og devices. Min Intune Konto har nå gått ut og når jeg koblet til en mobiltelefon til Office 365 eposten sin så fikk jeg feilmelding på mobilen under sync. Dette skjedde fordi sync policy’en lå i intune og siden intune var deaktivert så ville ikke han sende ut sikkerhetspolicy’en.
Svaret her var å fjerne policyen i Intune, vente på at Intune skulle synce med Office 365 (kan ta noen minutter) og så synce kontoen på nytt.
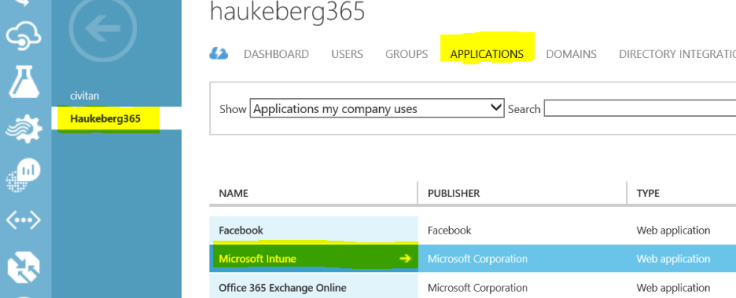
Nå i fremtiden må jeg koble vekk Intune fra Office 365 og det gjøres slik:
Dersom du ikke vil bruke Microsoft Intune så kan du koble vekk Intune slik:


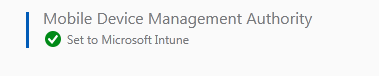
Hentet fra Peter Daalmans [MVP] http://configmgrblog.com/2015/05/14/hey-my-mdm-authority-is-set-to-office-365-in-microsoft-intune/
So, when I use my computer I like that it runs fast, cool and quiet.
All of a sudden disk starts whirr’ing and the system responds slower. Whats up?
Scheduled Windows Intune Endpoint Protection full scan is whats up.
Unfortunately for Intune, it can’t run while Your computer is off and since most People sleep their computer, they use it while its on.
Lets turn that stuff off…
Reference here: http://technet.microsoft.com/en-us/library/jj676574.aspx
Navigate to: http://manage.microsoft.com
Policies->Add New Policy->Windows Intune Agent->Tick: Create and Distribute Custom Policy->Create Policy
Name: Stop Scanning me
Search Plan -> Uncheck Both
Click “Save Policy”
On Promt->yes
Add Your groups->Click Ok
Tip: Also increase the time which you can delay restart after updates have been Applied to: 30 minutes

You must be logged in to post a comment.