Once you have:
you should be ready to deploly that script to computers running the Microsoft Intune Management Agent. The Intune MDM channel does not support EXE, only MSI.

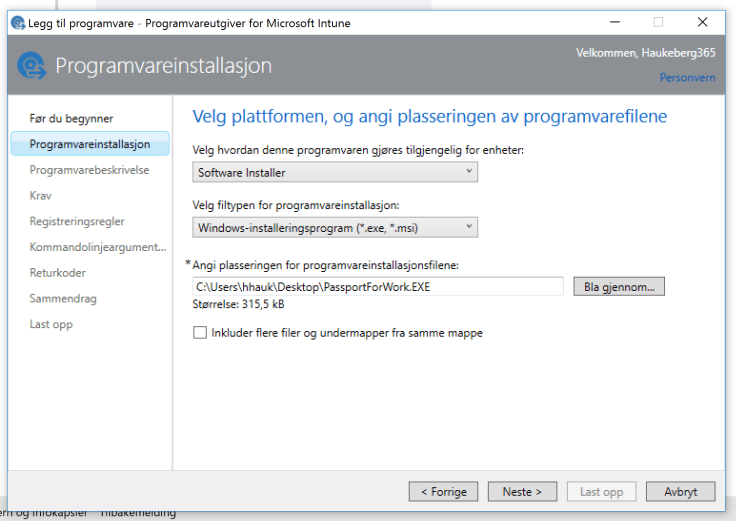
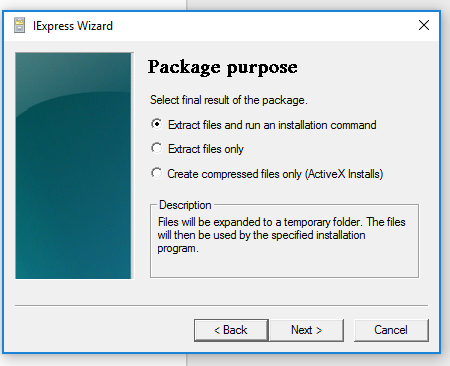
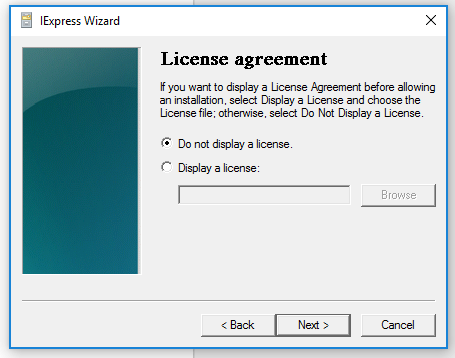
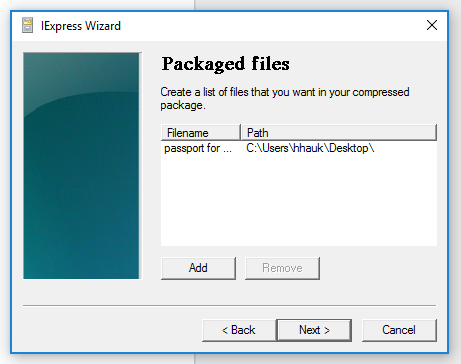
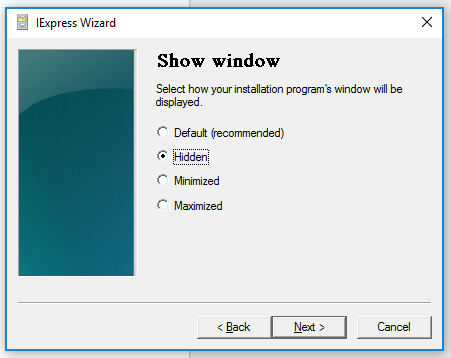
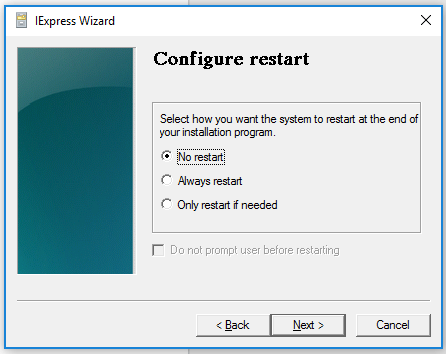
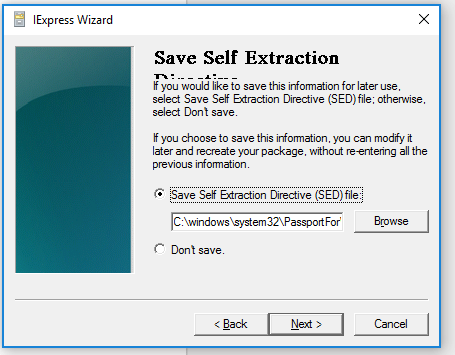
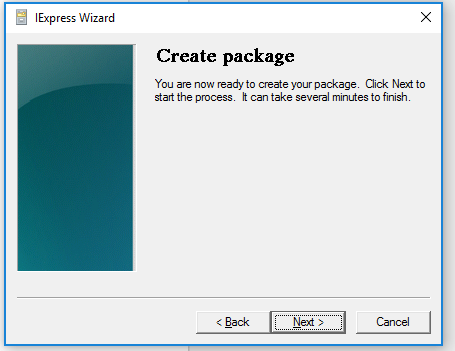
Follow the Wizard.


Once you have:
you should be ready to deploly that script to computers running the Microsoft Intune Management Agent. The Intune MDM channel does not support EXE, only MSI.

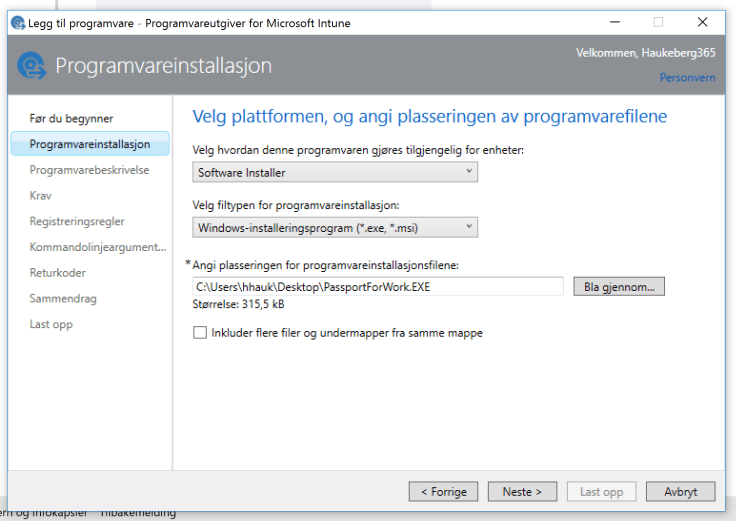
Follow the Wizard.


Microsoft Intune can not push out Group Policies onto computers, but we can target users or devices with scripts that change that setting in the registry.
Here is how you create a simple script that does just that.
@Echo off echo A Script to set a Registry value using Windows Intune REM registry key reg add HKLM\Software\Policies\Microsoft\PassportForWork /f reg add HKLM\Software\Policies\Microsoft\PassportForWork\ /v Enabled /t REG_DWORD /d 0 /f if errorlevel 1 ( echo Error installing reg key exit /b 1 ) else ( echo Installed regkey ) exit /b 0
Simply copy this script into a notepad file and then save it as PassportForWork.CMD right click and Run as Administrator to input the software policy where we set Passport for Work enabled as = 0 “Turn Off”
You can enter some of these register values:
REG_BINARY
REG_DWORD
REG_EXPAND_SZ
REG_LINK
REG_MULTI_SZ
Read more here: Registry Values (Technet)
Thanks to Richard Harrison at http://www.cableplugger.com/2013/03/adding-windows-registry-entry-with.html
Here is how you create a script that adds a registry setting to the computers managed by Microsoft Intune.
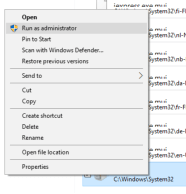
Navigate to:
C:\Windows\System32\iexpress.exe
Right click it and select “Run as Administrator”






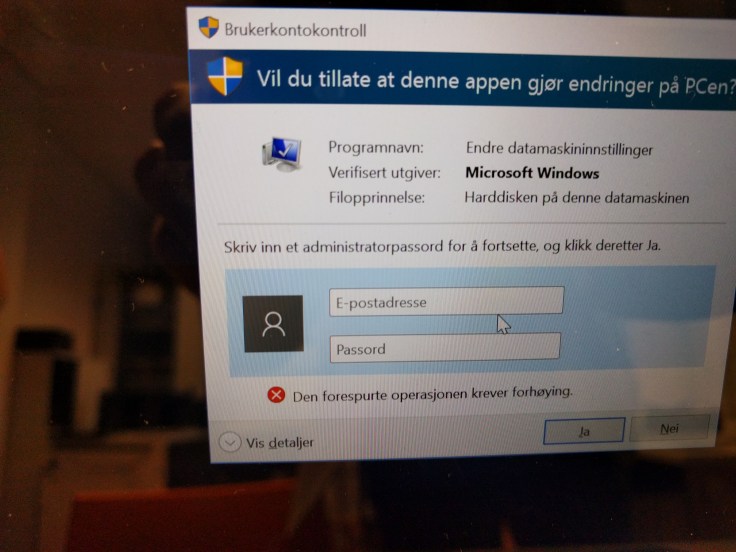
If you are stuck on this screen and forgot your login there is a simple way to reset your device.

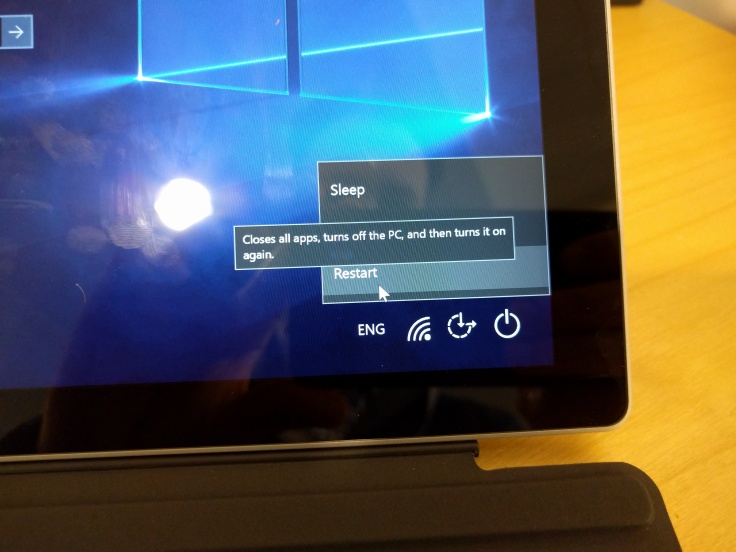
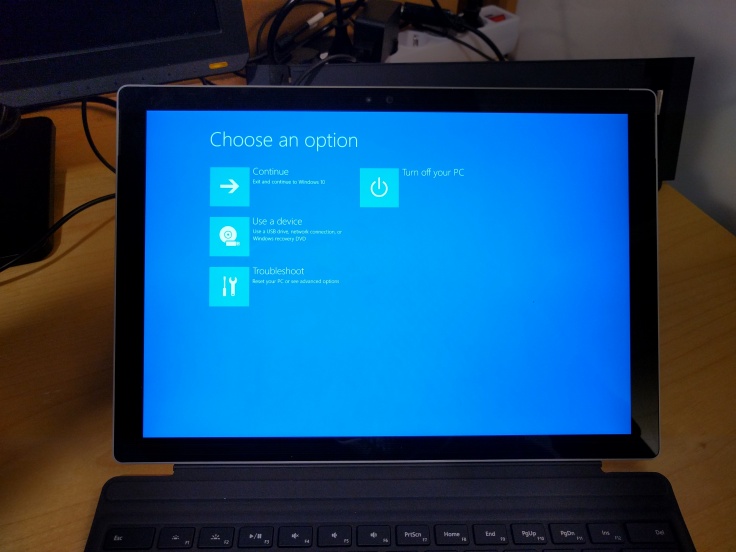
Thanks to: http://www.tenforums.com/tutorials/2294-advanced-startup-options-boot-windows-10-a.html
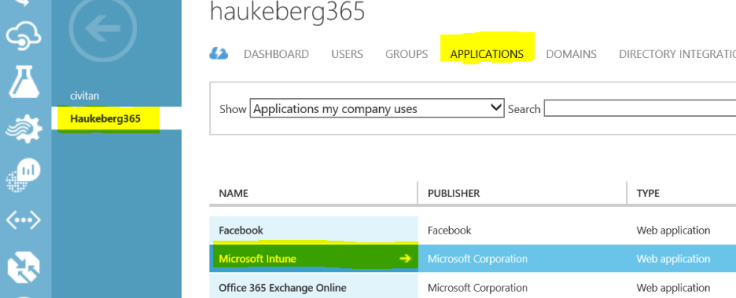
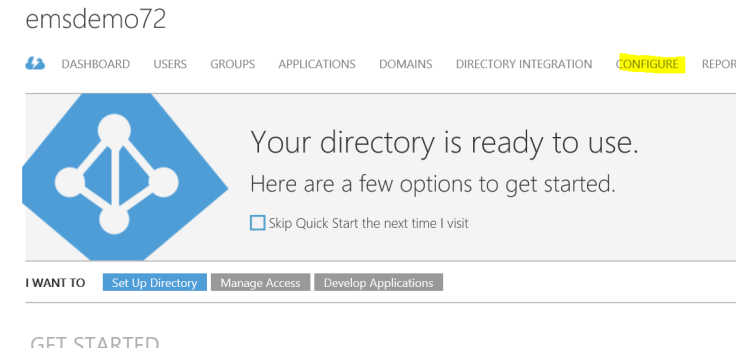
*THE AZURE AD PORTAL EXPERIENCE HAS BEEN UPDATED, TO FIND THIS SETTING IN THE NEW PORTAL LOOK HERE: Enable or Disable Windows hello in new AAD portal
If you are a larger organization or a school, simply asking your users to enter a pin and start authenticating with a phone might be challenging. Even more so when they have never done that before.
Here is how you disable PIN challenge and phone verification when joining Azure AD
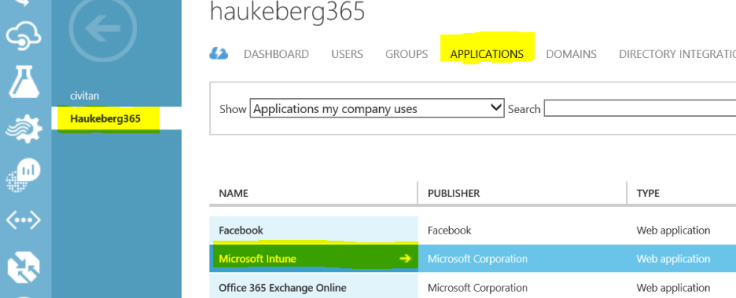
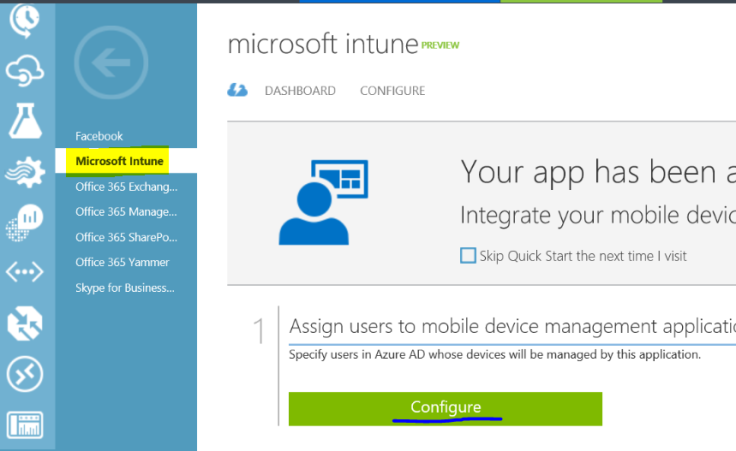
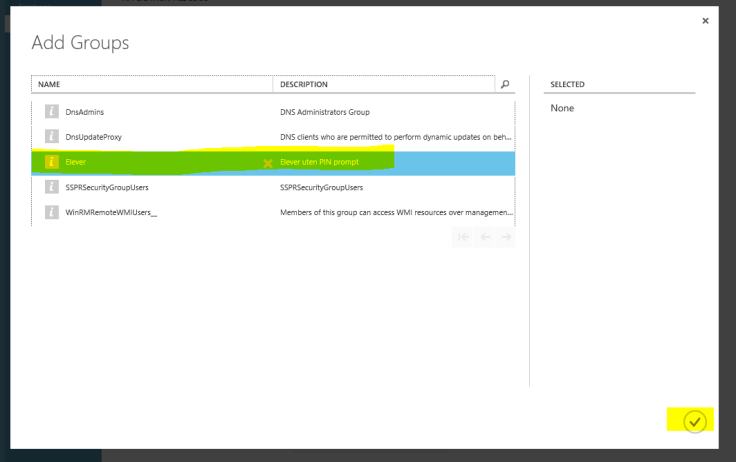
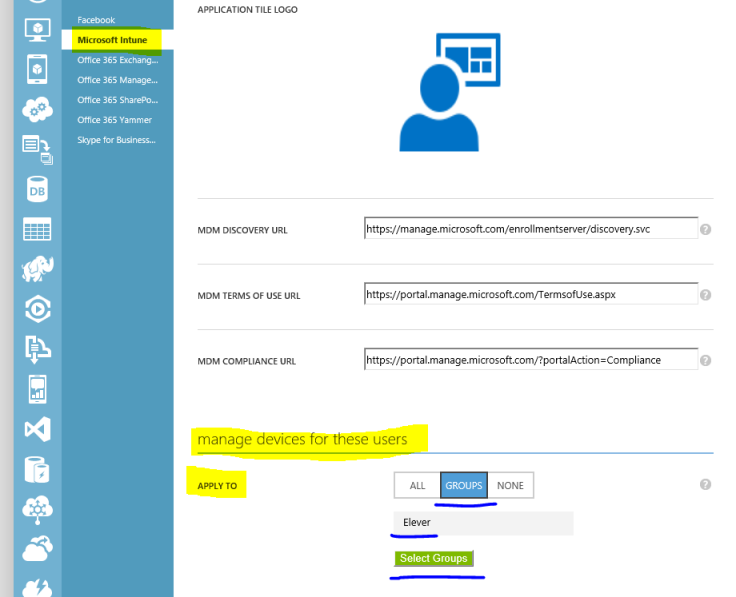
UPDATE: In Azure.
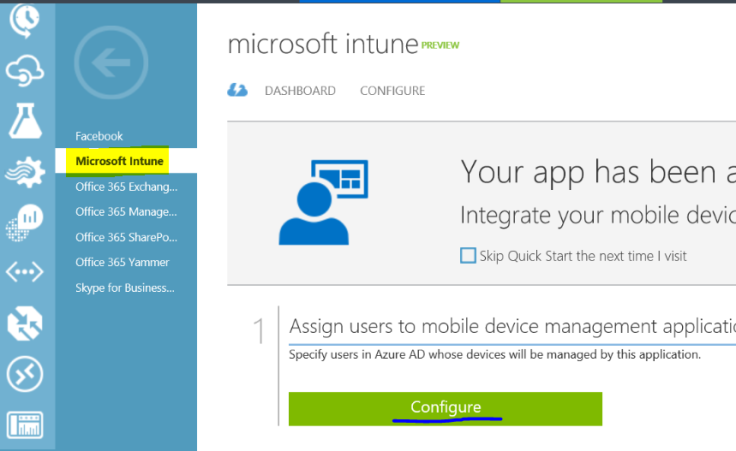
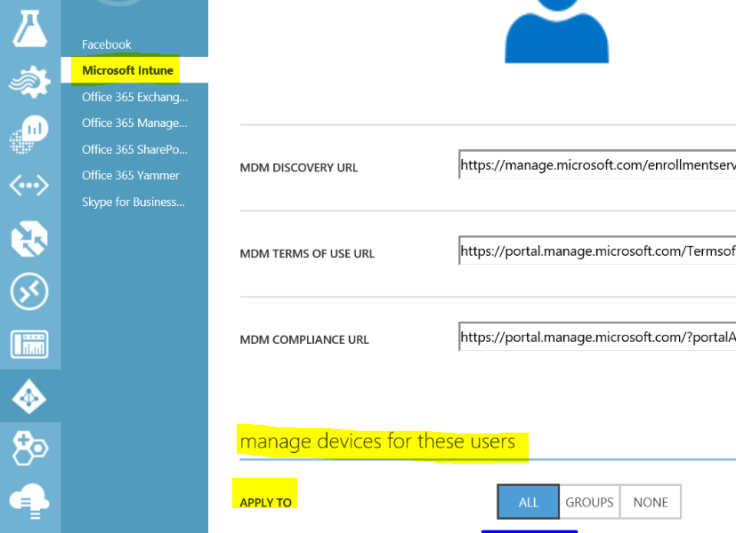
In Intune.
Thats it.
You can join Azure AD and use the Intune device agent for MDM and not the MDM channel when you enroll. It is a bit tricky and require manual touch on the device.
The best experience is to include the Intune agent in the Windows Image. If can not do this then here is how:
In Azure AD:
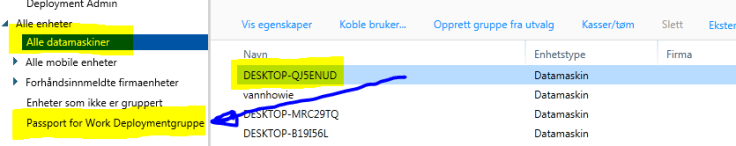
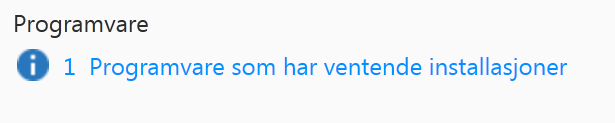
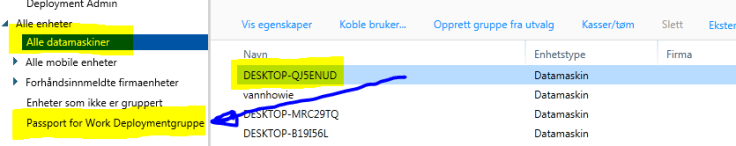
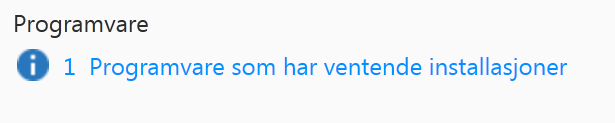
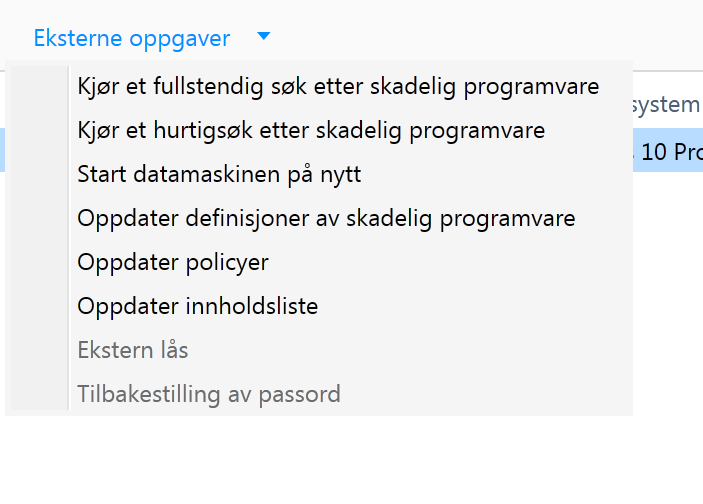
In Intune:
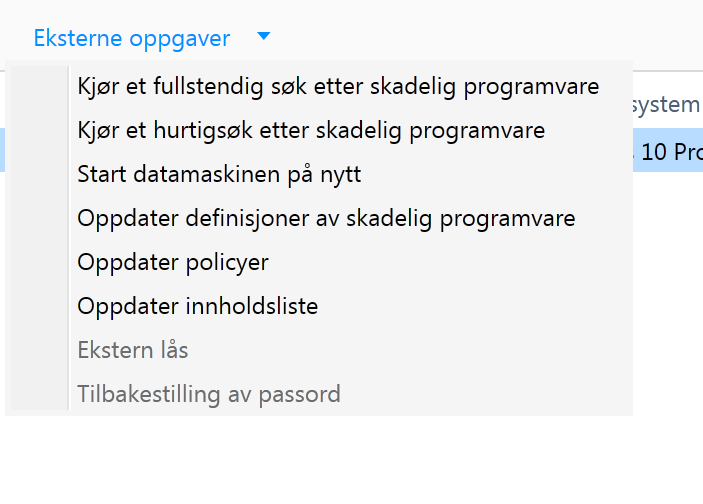
On the Device:
You can configure Microsoft Intune to block devices that do not comply with a “standard” access to Office 365 Exchange Online email.
Here is how:

The iOS users will now have to enroll in order to read email and when they do they need to set a 6 digit password.
Caution with using Active Sync only:
Enrollment procedure:
When you have more users than devices or users share devices and you only have Azure Active Directory the ability to switch users work a bit differently.
The first user that you enroll with will be an Administrator, all subsequent users will be a Standard users.
Microsoft Intune will block any user to enroll a multitude of devices. The limit is set in Azure Active Direcory at 20 Devices. You can change this.
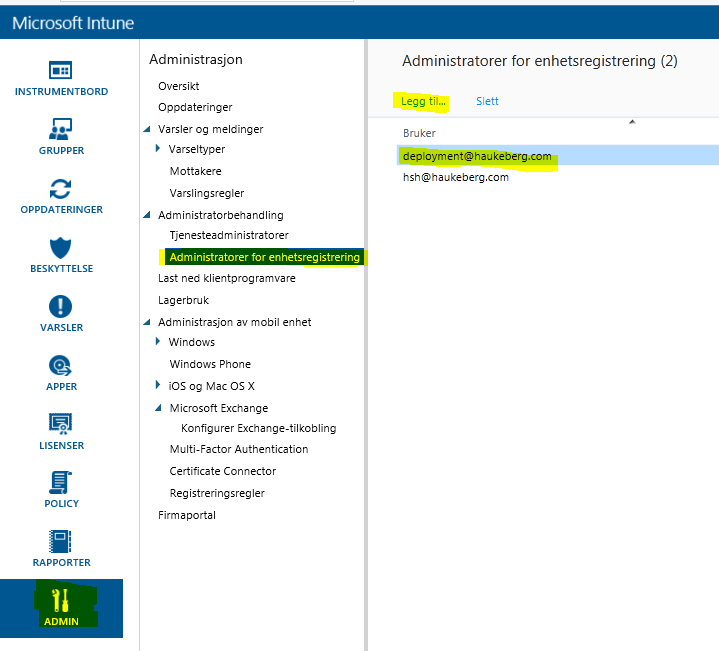
To do this keep in mind that you need to be an Administrator:
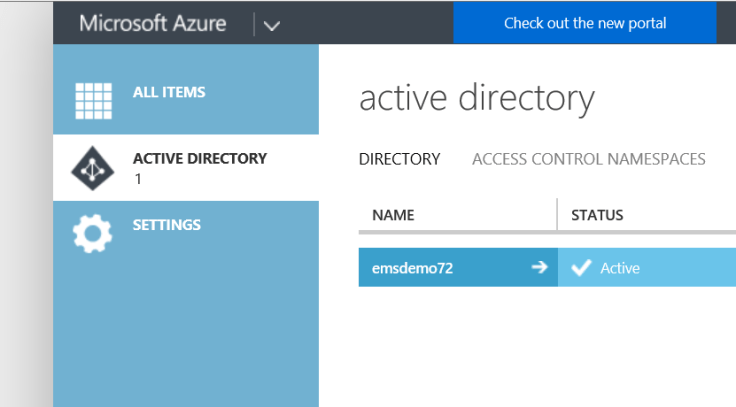
Navigate to: http://manage.windowsazure.com

That is it. This user can now enroll an 1000 devices. on this domain
In Windows 10 you can join a machine to Azure AD instead of a local domain.
But
When you join Azure AD your account is given administrator privileges automatically. If you switch users by Ctrl+Alt+Del and Switch user, that user is set as a Standard user.
If you do not know who will use the computer, only the first user will be administrator, the rest will be standard users and can not install programs.
This action is default and can not be changed. Simply giving machines out to students will result in the first users becoming administrators. If you boot all machines before deployment and log in with your user, that user will be blocked after about 20 devices.
How to fix this? Take a look at this post: https://haukeberg.wordpress.com/2016/01/18/shared-devices-roaming-profiles-with-microsoft-intune/
You must be logged in to post a comment.