If you want to know how users are consuming Azure MFA or Self Service Password Reset this is where you find that info:
Self Service Password Reset log:
- Go to http://manage.windowsazure.com
- Click on Directory
- Click on your Azure AD directory
- For SSPR click here:

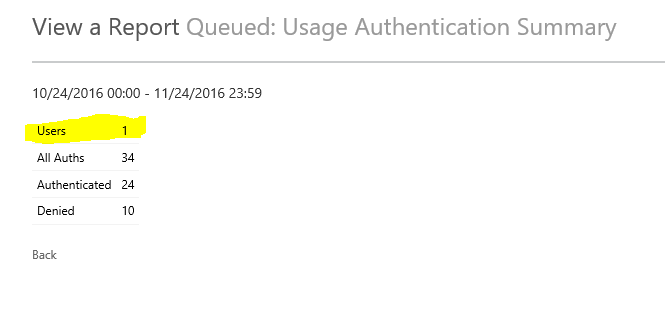
For Azure MFA activity log:
- Go to http://manage.windowsazure.com
- Click on Directory
- Click on your Azure AD directory
- Click Configure
- Scroll Down to Multi-Factor Authentication and click: Manage Service settings
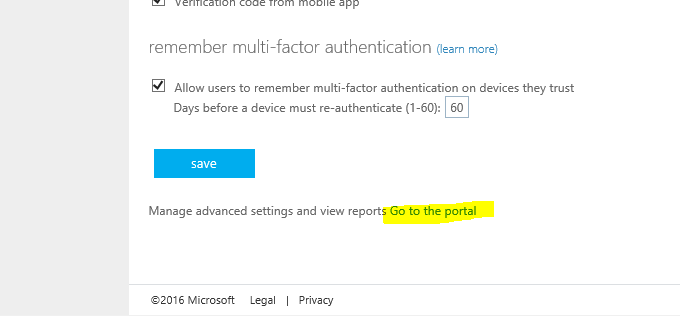
- Click “Go to the Portal” at the very bottom
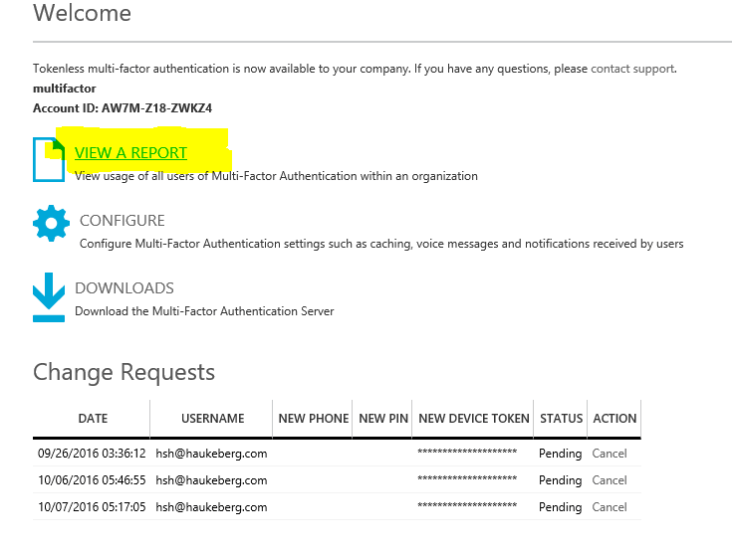
- Click View Report
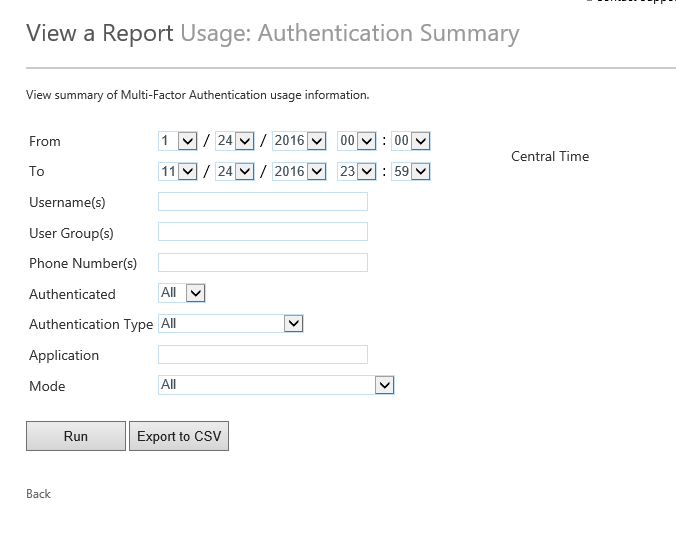
- Click Summary
- Select 1 month back
- Click Run
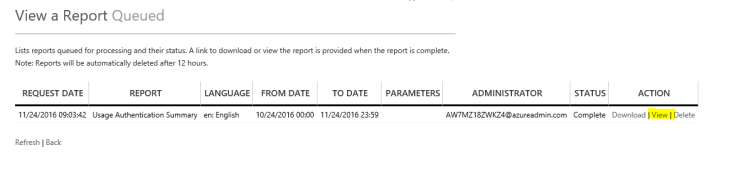
- Go to Queued Reports
- Click on View Report
You can also see reports sorted on users and how much they log in.



















You must be logged in to post a comment.